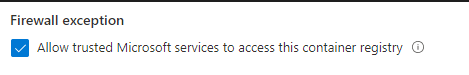
Since releasing the ”Firewall exception” for trusted Microsoft services, you can now allow Azure Defender to access the container registry for image scanning, while also restricting access to Azure Container registry via firewall
- Allowing Defender for ACR to scan container images via ’Trusted service’ setting on firewall
- Allowing AKS to Pull images from ACR using load balancer public IP
- This is not the only config option, there is also version using private endpoints. I personally prefer using public endpoints, as there is less to configure and maintain (not that would not have it’s use cases)
Background
Config for AKS cluster with Azure CNI and Azure Standard Load Balancer
| Task | Status | Location |
|---|---|---|
| Allow access from Azure Security Center for Image Scanning | ✅ | ACR Networking – Firewall |
| Allow access from AKS outbound Loadbalancer | ✅ | ACR Networking – Firewall |

MS Docs References
| Source | Task | Info | status |
|---|---|---|---|
| MS Docs Azure Policy | Configure container registries to disable local authentication. | Disable local authentication so that your container registries exclusively require Azure Active Directory identities for authentication. Learn more about at: https://aka.ms/acr/authentication. | ✅ |
| MS Docs Azure Policy | Container registries should not allow unrestricted network access | Azure container registries by default accept connections over the internet from hosts on any network. To protect your registries from potential threats, allow access from only specific public IP addresses or address ranges. If your registry doesn’t have an IP/firewall rule or a configured virtual network, it will appear in the unhealthy resources. Learn more about Container Registry network rules here: https://aka.ms/acr/portal/public-network and here https://aka.ms/acr/vnet. | ✅ |
Verifying configuration
On successful configuration you should see that the AKS loadbalancer IP, and Azure Security Center both can access the ACR.
// Show registry events reported over the last hour // A list of registry event logs, sorted by time (earliest logs shown first). ContainerRegistryRepositoryEvents | where TimeGenerated > ago(24h) | sort by TimeGenerated asc | distinct CallerIpAddress, ArtifactType, OperationName, Identity

0 comments on “Restricting Access to Azure Container Registry from AKS while allowing Azure Defender Access”