Blog preview – full write-up pending.
One of my personal typical failures at monitoring is when I realize I have not enabled Diagnostic Settings for a resource in Azure… Typically I either want to debug, or have just tested something security related against the resource, and realize, that there are no logs available…
I got fed up with finding out that logs are not enabled, and created quick solution that does not require active maintenance of Azure Policies
Options
- If you have proper Cloud Governance model in place, you can use Azure Policy to deploy diagnostic settings, while you also deploy other policy enforcements for the resource
- Use Azure Resource Manager API, Azure Event Hub and Azure Functions to dynamically populate Diagnostic settings for resources
I choose nr 2. because option 1 requires actively adding policy definitions for each new resource type
- Option 1 is the best way to do this, but requires relatively good maturity on organizations governance policies. I wanted to test how far I can go with automation of Azure Resource Manager
- Option 2 will use the ’diagnosticSettingsCategories’ applicability (not all resources are applicable) to dynamically deploy ”diagnosticSetting” for such resources
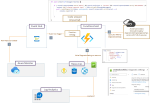
Architecture
Click the picture below for PoC architecture media file
Results
After adding new resource to Azure it takes few mins, after which the diagnostic Settings are populated for the resource.
Application insights logs will correlate with any applicable resource that has been updated for security logs


0 comments on “Blog Preview – Automatic enablement of diagnostic settings for security logs”