You might see the following recommendation in Azure Security Center (Assuming you have enabled the security center add-on for AKS).
I did short write-up how such credentials are used from possibly compromised POD
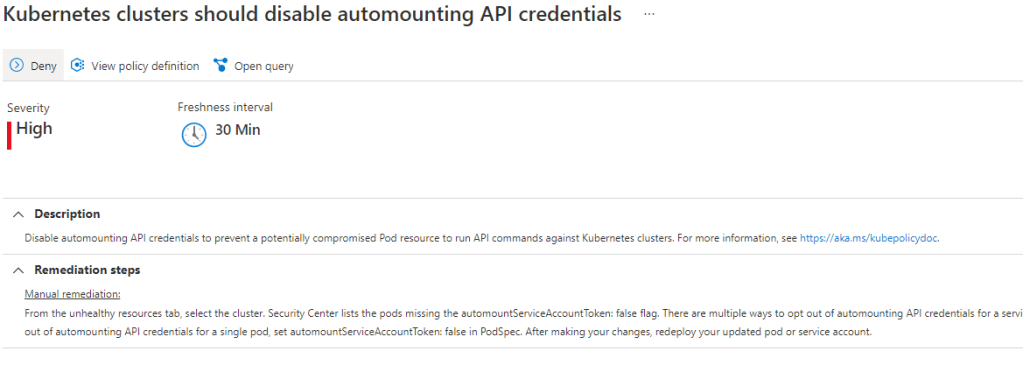
[ASC] Kubernetes clusters should disable automounting API credentials
Disable automounting API credentials to prevent a potentially compromised Pod resource to run API commands against Kubernetes clusters.
How the feature works from POD side?
- You should see credentials when checking:
kubectl exec "yourPod" -n "namespace" cat /var/run/secrets/kubernetes.io/serviceaccount/token - if you see credentials then the default POD identity can query the api server
## --insecure if you dont want to read the CA cert...
curl --header "Authorization: Bearer ${TOKEN}" -X GET https://kubernetes.default.svc/api/v1/ --insecure
Investigation
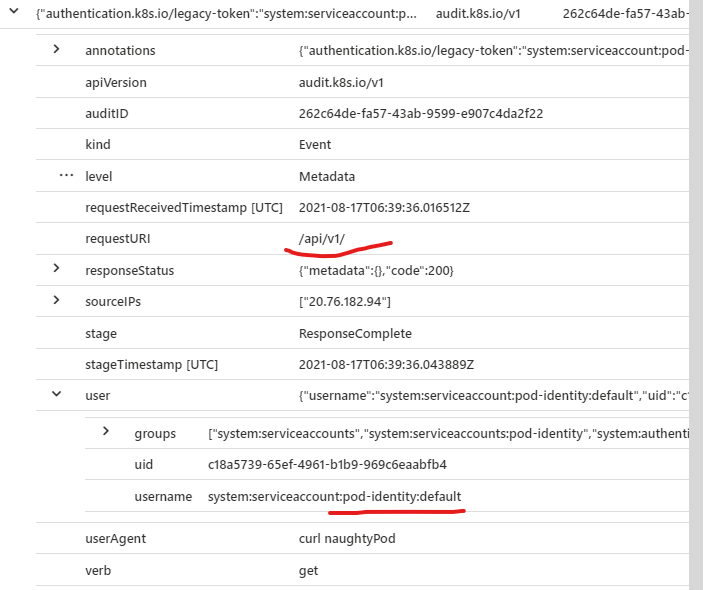
- You can read such events from Azure Log Analytics (Or Sentinel enabled workspace)
- Example read where the attacker is using CURL from the compromised POD
AzureDiagnostics
| where TimeGenerated > now() - 10min
| extend auditL = parse_json(log_s)
| where auditL['requestURI'] contains "api"
| where auditL['userAgent'] contains "curl"
| project auditL
| evaluate bag_unpack(auditL)
Mitigation
Kubernetes versions since 1.6 allow settings the ”automountServiceAccountToken” to false
#From AKS documentation (Source below)
apiVersion: v1
kind: ServiceAccount
metadata:
name: build-robot
automountServiceAccountToken: false
Sources
MS Security Center
https://kubernetes.io/docs/tasks/run-application/access-api-from-pod/
0 comments on “Azure AKS – Reviewing recommendations from Security Center – Disabling Automounting API Credentials”