AAD API App Registrations Client Credentials Client Credentials Certificate Authentication code JWT Validation NodeJS On-Behalf-Of flow VsCode
Securing Client Credentials Flow with Certificate
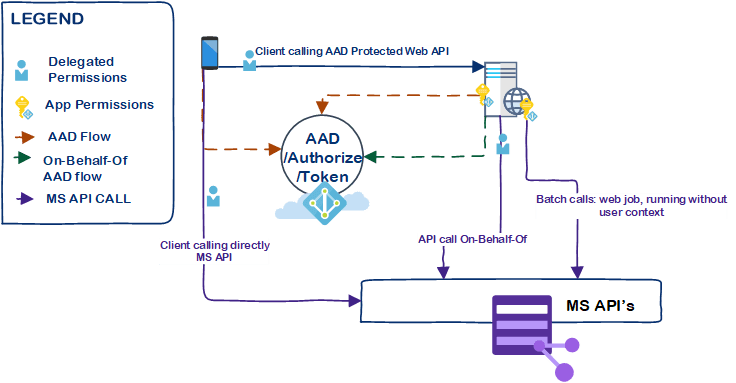
Sometimes there is application which requires background jobs to run without user interaction (though in most cases you can manageLue lisää