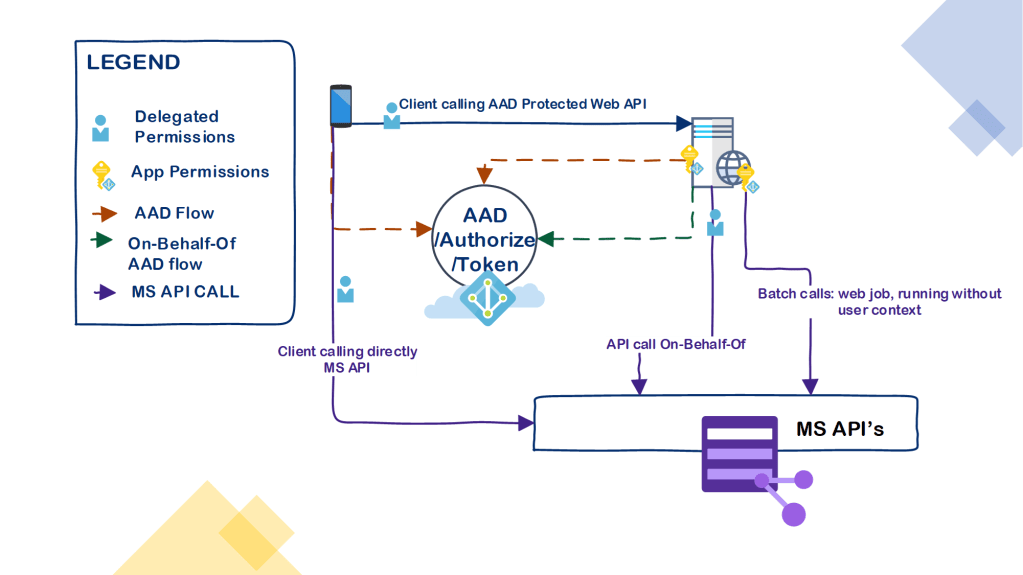
Sometimes there is application which requires background jobs to run without user interaction (though in most cases you can manage to avoid using App Permissions) In these particular exceptions using app permissions and client credentials might be justified, especially if you don’t want to maintain (and secure) long term storage of user refresh token for non user context operation.
Prevalent use of Shared Secrets in Client Credentials
I often see Client Credentials used with shared secret, and do understand that for some SaaS integrations with self service of on-boarding the shared secret is the easy way to on-board them. (Although uploading the private key for the particular app is not rocket science either, could be easily used in most of the cases)
Why Certificate is better than Shared Secret
- Certificate Credentials never transmit the plain-text secret when requesting Access Tokens from Azure AD. Instead they transit JWT token which is signed with private key which the app holds. Verification is asymmetric, so Azure AD holds only the key which can assert that the JWT token came from the party in posession of the private key
- Shared Secret in essence is weaker verification method (String vs Certificate)
- You have more established ways to protect the certificate, than a single string
Updated example
Node.js GitHub Repo: Azure AD Client Credentials With Certificate
Alternatives to a certificate
- You can use API management in conjunction with JWT-Bearer flow to gain better control of Shared Secret of 3rd parties.
- This could be done by restricting caller IP’s and using several policies concerning the use Partners given access to Client Crendentials. In this scenario API management forwards the token once policies are checked
- You could put short lived (few days) Client Secret in a Key Vault, and authorize the Key Vault answer only to a certain trusted IP’s… Still…once the plain text is exposed in the code run time the Client Secret is out of Key Vaults Domain until the client secret expires
- Generally Client Secrets aren’t meant to be used as short lived
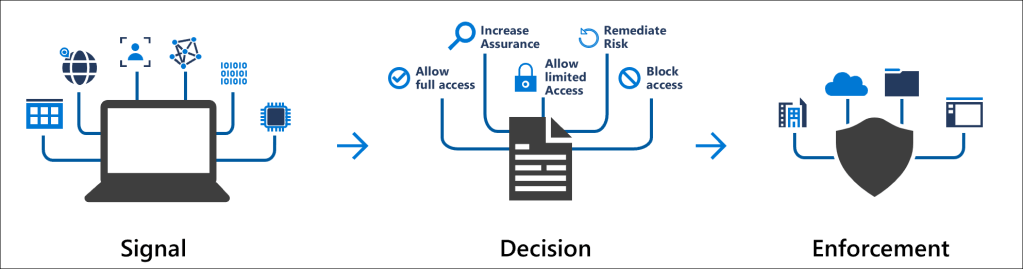
- … And if the API doesn’t need App Permissions, you can use Conditional Access…
- You shouldn’t use real user service account as service account just get conditional access. Using a user principal instead of actual service principal opens another set of problems, which this blog is too short to delve on
Updated example here
Updated example
Node.js GitHub Repo: Azure AD Client Credentials With Certificate
Enable NodeJS API for Client Credentials with Certificate
Before proceeding using App Permissions, or Shared Secret in any other flow just check that your scenario is not one of the below Examples
- App Permissions used in flows that could’ve used delegated permissions using users token context
- Mobile Client Using Client Secret as part of Authorization Code Flow (Mobile client is not confidential client, lets just leave it there)
- (Not directly related, but a concern) App Permissions are required by multi-tenant app
- In most scenarios you can create additional single tenant app, besides the registered multi-tenant to retain control of the shared secret (revokation etc).
- Giving external multi-tenant app permissions is something you should think hard before proceeding in the first place
- In most scenarios you can create additional single tenant app, besides the registered multi-tenant to retain control of the shared secret (revokation etc).
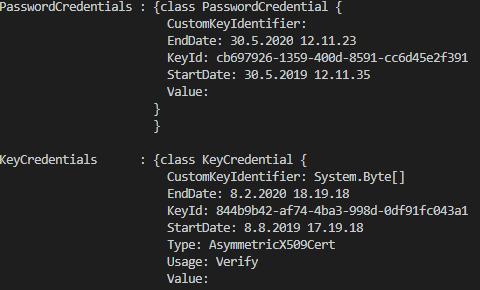
Create Certificate Credentials for existing App Registration
Pre-hardening
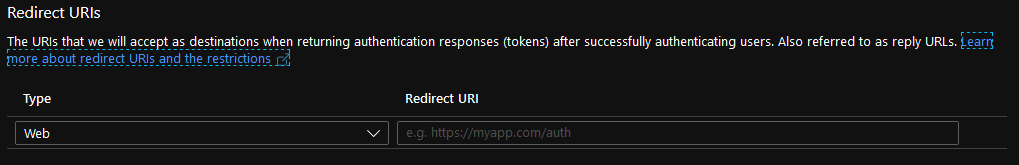
- Ensure Application doesn’t have any redirect URI’s. This effectively ensures no user sign in process can get tokens returned for the Application
- Remove the default delegated user permissions from the app
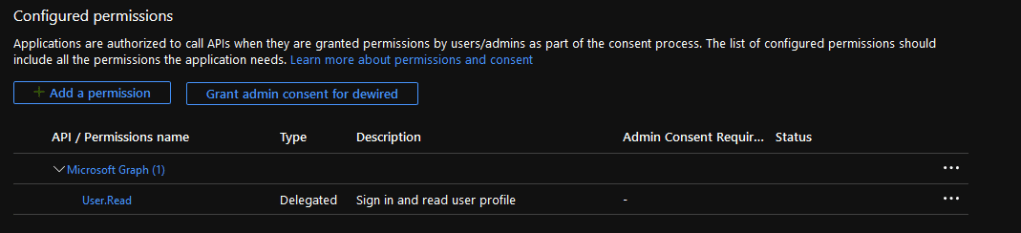
- Ensure Implicit Grant isn’t enabled in the application (This wouldn’t work any way with the user permissions removed to sign-in and read user profile , but we do some additional cleaning here)
- Remove Any password credentials app might have (obviously, if they are used production, dont remove them until the flow is updated to use certificate in code for these apps)
Pre-reqs
- OpenSSL binaries
- Azure AD PowerShell Module
$Subject = "CN=" + "DemoApplication2"
$Expiration = (get-date).AddYears(2)
$pass = Read-Host -Prompt "PFX exporting Password"
$cert = New-SelfSignedCertificate -CertStoreLocation "Cert:\CurrentUser\My" -Subject $Subject -KeySpec KeyExchange -NotAfter $Expiration
$AADKeyValue = [System.Convert]::ToBase64String($cert.GetRawCertData())
$cert| Export-PfxCertificate -FilePath (($Subject -split "=")[1] + ".pfx") -Password ($pass | ConvertTo-SecureString -AsPlainText -Force)
#Navigate to directory where OpenSSL is installed
.\openssl.exe pkcs12 -in (($Subject -split "=")[1] + ".pfx") -passin "pass:$pass" -out (($Subject -split "=")[1] + ".pem") -nodes
$data = get-content (($Subject -split "=")[1] + ".pem")
$data[$data.IndexOf("-----BEGIN PRIVATE KEY-----")..$data.IndexOf("-----END PRIVATE KEY-----")] | Out-File (($Subject -split "=")[1] + ".pem") -encoding "DEFAULT"
connect-azuread
$application = New-AzureADApplication -DisplayName ($Subject -split "=")[1]
New-AzureADApplicationKeyCredential -ObjectId $application.ObjectId -CustomKeyIdentifier ($Subject -split "=")[1] -Type AsymmetricX509Cert -Usage Verify -Value $AADKeyValue -EndDate ($Expiration | get-date -format "dd.M.yyyy" )
NodeJS Code Example using ADAL and Certificate Credentials
- In the code fill the thumprint, clientID (appid), and your tenant name
//Gets Access Token by sending private key signed JWT Token to Azure AD Token Endpoint
//https://docs.microsoft.com/en-us/azure/active-directory/develop/active-directory-certificate-credentials
//https://www.npmjs.com/package/adal-node
const {AuthenticationContext,Logging} = require("adal-node")
//set logging level to verbose, and print to console
Logging.setLoggingOptions({
log: (level, message, error) => {
console.log(message)
},
level: Logging.LOGGING_LEVEL.VERBOSE,
loggingWithPII: true
});
//Token Request Options
var options = {
URLwithTenant:"https://login.windows.net/dewired.onmicrosoft.com",
resource:"https://graph.microsoft.com",
applicationId : "c81ea829-d488-46c2-8838-68dde9052478",
certThumbPrint:"72B807BE590A73E0B88947C902C5C58E22344C5F"
}
'
var context = new AuthenticationContext(options.URLwithTenant);
//Read Certificate from buffer to UTF8 string
const fs = require("fs")
var keyStringFromBuffer = fs.readFileSync("DemoApplication2.pem").toString("UTF8")
console.log(keyStringFromBuffer)
//acquireToken
context.acquireTokenWithClientCertificate(options.resource,options.applicationId,keyStringFromBuffer,options.certThumbPrint,(error,tokenresponse) => {
console.log(error,tokenresponse)
})
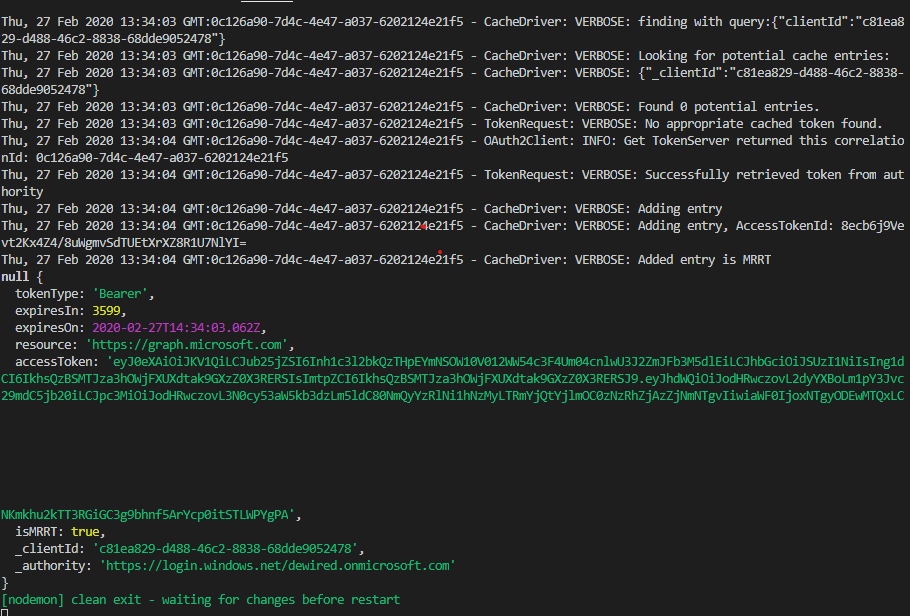
In the end you should see verbose message with token returned in the callback for tokenResponse.
If you see error about the self signed cert, ensure that all localization settings match UTF8, and that there are no empty space characters in the PEM file. If you still see the error, copy the Private Key manually from the openSSL created file
Br, Joosua



0 comments on “Securing Client Credentials Flow with Certificate”