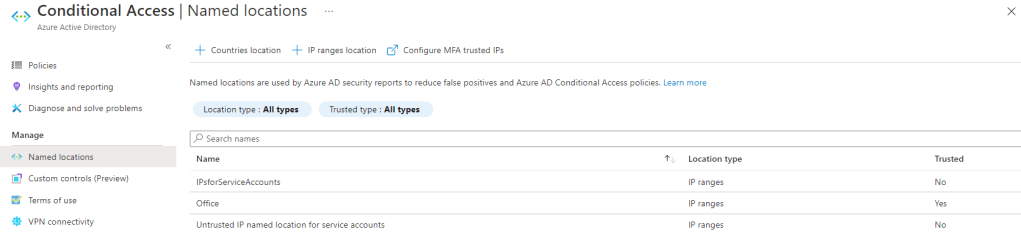
Azure AD logs contain NetworkLocationDetails property, which contains information if network is tagged as trusted named location, or just named network location in Conditional Access.
Use cases
- It’s much easier to understand why and how Conditional Access Policy is targeted, or bypassed (Exclusion) condition, since the logs contain now extra information about the named location in the NetworkLocationDetails property
- Having a quick way to see when events in logs are being generated in tagged networks (named locations)
Background
If you are interested about generally the themes here, I recommend reviewing following articles
Locations
Location condition in Azure Active Directory Conditional Access | Microsoft Docs
Log Analytics
bag_unpack plugin – Azure Data Explorer | Microsoft Docs
mv-expand operator – Azure Data Explorer | Microsoft Docs
Example queries
Expand unique NetworkLocationDetails to simple columns with sign-in logs information
- Expands records with networkLocationDetails populated for selected projection
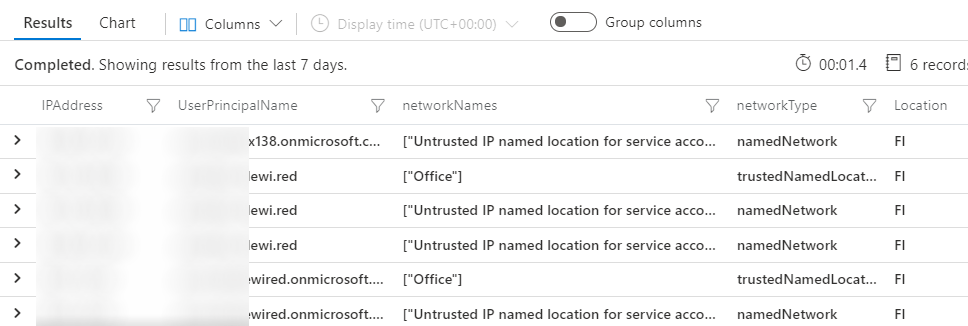
union AADNonInteractiveUserSignInLogs, SigninLogs | project NetworkLocationDetails, IPAddress, UserPrincipalName, Location | mv-expand parse_json(NetworkLocationDetails) | evaluate bag_unpack(NetworkLocationDetails) | distinct IPAddress, UserPrincipalName, tostring(networkNames), networkType, Location
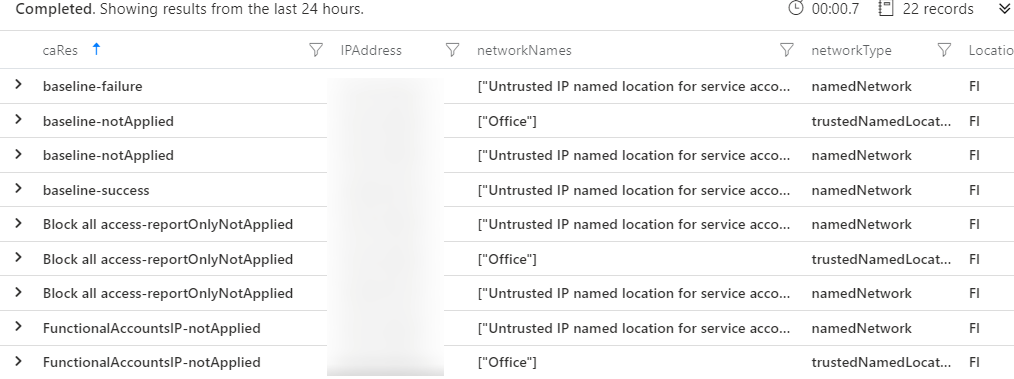
Expand unique NetworkLocationDetails side by side with Conditional Access Results
union AADNonInteractiveUserSignInLogs, SigninLogs | mv-expand parse_json(NetworkLocationDetails) | evaluate bag_unpack(NetworkLocationDetails) | extend CaDetail = iff(isempty(ConditionalAccessPolicies_dynamic) == true, parse_json(ConditionalAccessPolicies_string), ConditionalAccessPolicies_dynamic) |mv-expand CaDetail | extend caRes = strcat(CaDetail.displayName, '-', CaDetail.result) | distinct IPAddress, tostring(networkNames), networkType, Location, caRes
End of blog
With various real world use cases you can optimize and tune the queries as you want. These were just technical examples showing how to get started with the information provided
Hello,
I don’t find the fields ConditionalAccessPolicies_string our _dynamic
Would you mind explaining a bit more
Thanks
TykkääTykkää
Hi Christophe! The queries use UNION operator, which takes input of two different tables (SigninLogs and NonInteractive) – both of those logs contain information for ConditionalAccessPolicies, but types are different for these sources (String, and dynamic), thats why the output of UNION operator will in these cases produce two records instead of one. My query, just normalizes them
TykkääTykkää