ControlId
AzureAD_AppSvc_danglingRedirectUri
Category
Authentication, Spoofing
Description
Redirect URI’s pointing to myapp.azurewebsites.net in Azure AD App Registrations should always point to customer controlled App Service instance.
Malicious use case: If the app service is deleted, but redirect_uri is not deleted from the Azure AD app registration, attacker could register the App Service instance for malicious intent. After registering the App Service instance Attacker would then redirect user sessions authorization codes/tokens to attacker controlled service.
Detection of dangling redirect_uri
Depedency AzureAd PS Module
- Performs scan to see if the fqdn is not registered in DNS for potential subdomain takeover.
- If the FQDN is already registered, no result is given, and it’s assumed, that the record is registered in customer tenant. The script does not check if the fqdn is already compromised.
Connect-AzureAD
$apps = Get-azureAdApplication -All $true
$mta = $apps|
Where-Object {$_.ReplyUrls -match "azurewebsites.net"} |
Select-Object -ExpandProperty replyurls | Where-Object {$_ -match "azurewebsites.net"}
$list = @()
foreach ($domain in $mta) {
if ($domain -match "http://") {
$list+=($domain -split "http://" -split "/")[1];
}
if ($domain -match "https://") {
$list+=($domain -split "https://" -split "/")[1];
}
}
$results = @()
$ErrorActionPreference = "Stop"
foreach ($parsed in $list) {
try {
$s = Resolve-DnsName $parsed;
}
catch {
Write-Host "Subdomain takeover possible for $parsed" -ForegroundColor red
$ob = $apps | where {$_.ReplyUrls -match $parsed}
$ob | Add-Member -NotePropertyName "subdomain_takeOverPlausible" -NotePropertyValue $parsed -Force
$results += $ob
}
}
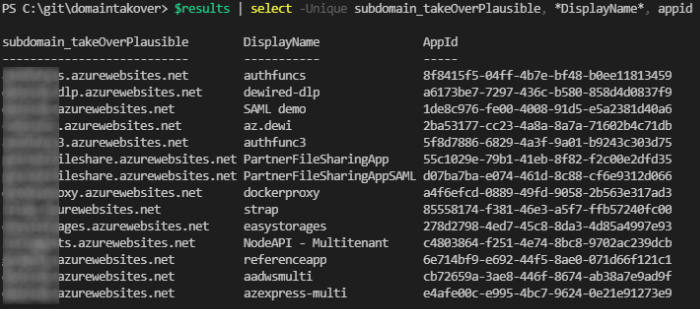
$results | select -Unique subdomain_takeOverPlausible, *DisplayName*, appid
Mitigations
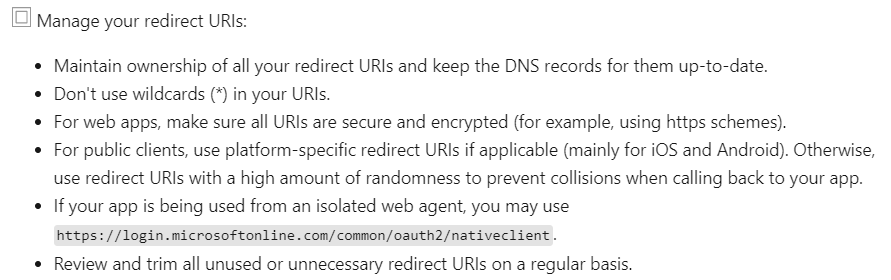
The first mitigation should always be stringent management and clean-up of redirect_uri’s.
- If the client is confidential client (requires client secret to exchange authorization code to token ) the attacker would not be directly able to exchange the code to token. Attacker could pass the authorization code to the legitimate service and get token in return.
References
This attack is similar to the one described in the following docs article: subdomain takeover with the distinction, that it does need any cname record pointing from customer owned domain to the attacker controlled service. The attacker still needs to supply the link to victim, in latter scenario.

0 comments on “Using PowerShell to find dangling Redirect URI’s in Azure AD Tenant”