I’ve recently had few discussion about tenant-wide consents, and how some companies would like to ensure, that admin consents don’t result in granting permission to all principals in the tenant.
Solutions
For our solution the background is typically admin consent requiring scenario, or scenario where admins want users to avoid consent prompt, without consenting for the whole tenant.
While there are many ways to handle this; I am presenting admin controlled approach, which results in adding the permission for just single user and permission object, instead of granting permissions for the entire tenant.
- My idea was to create simple web app to provide GUI for admins performing addition of these permissions.
Tooling
I created a small NodeJS web app that interfaces with Graph API ’oauth2PermissionGrants’ resource to populate the desired permission for the user with the app
Workflow
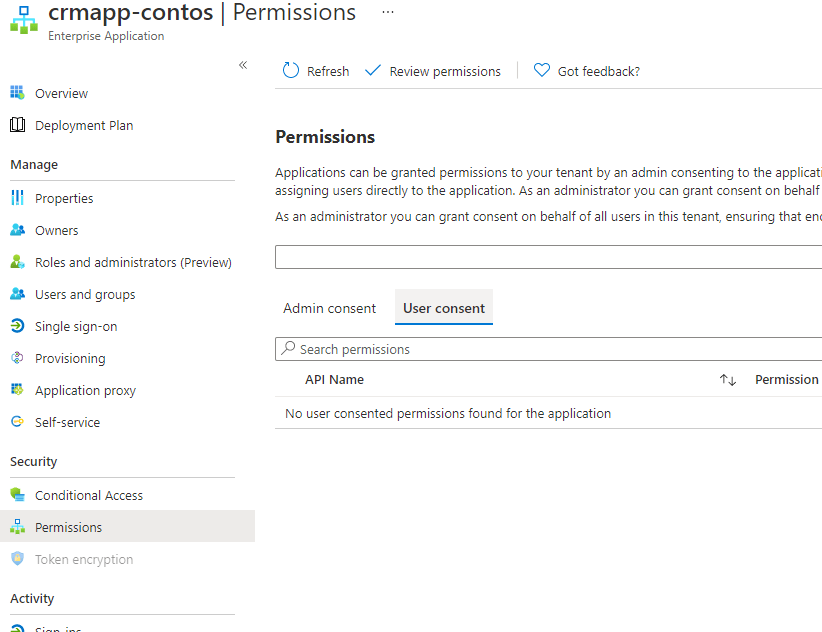
This is starting state of the application permissions (admin and user consents are empty)
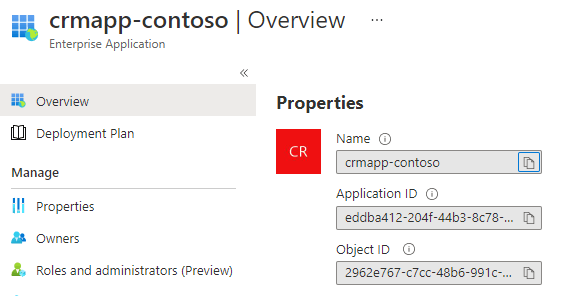
- Admin is signed in the app with their own admin context (Scope is Directory.AccessAsUser.All)
- Admin uses the ObjectID of the Azure AD Application, and resourceID (in this case of AzureAD, as permission requested is for) Directory.Read.All
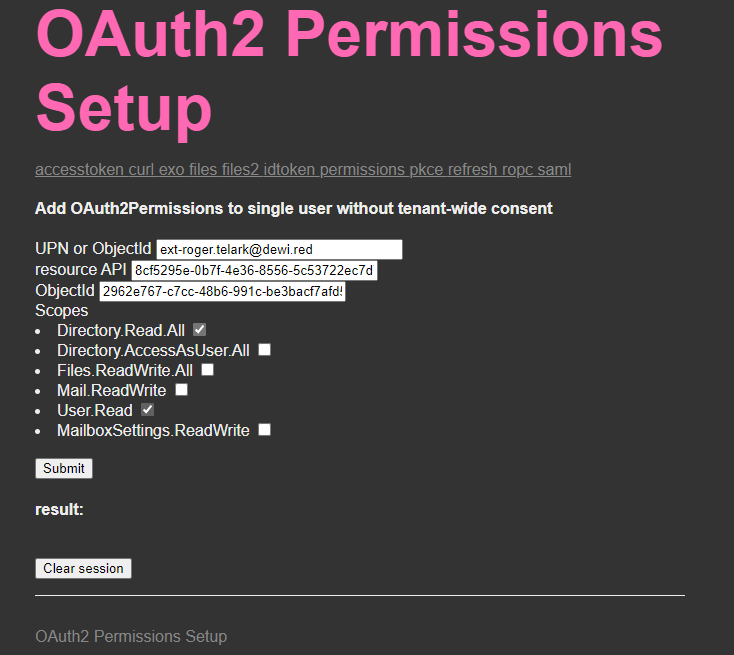
- Admin submits the API request
- Result shows the added object in the NodeJS app

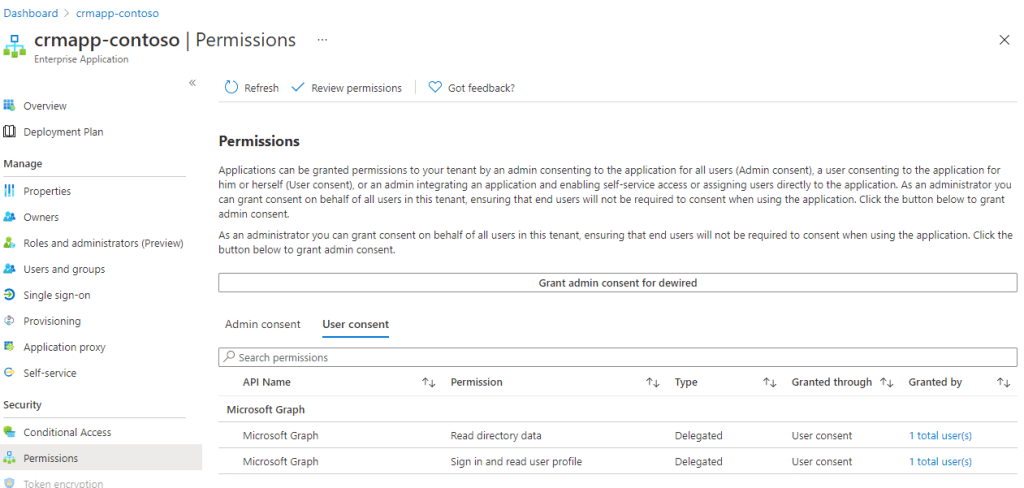
- Change is also reflected in the permissions section of the enterprise app
References
The following blog was tip given by one of my industry peers
How to grant permissions to users to use the Azure AD connector in Flow – Alex Tofan’s blog
0 comments on “PoC – Grant Azure AD OAuth2 Permissions without tenant-wide consent”