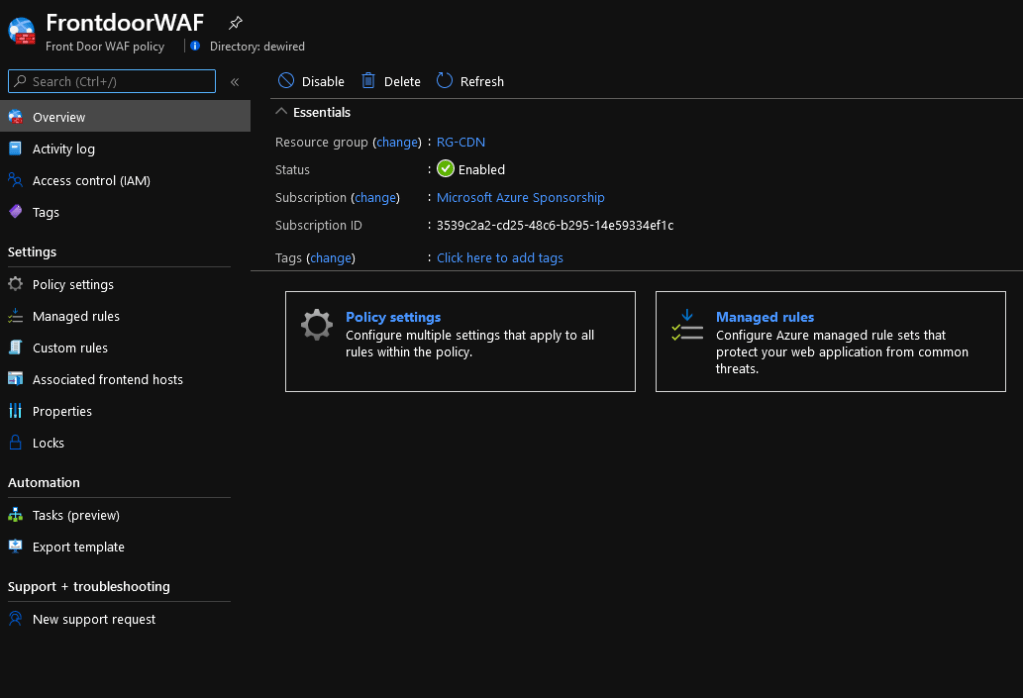
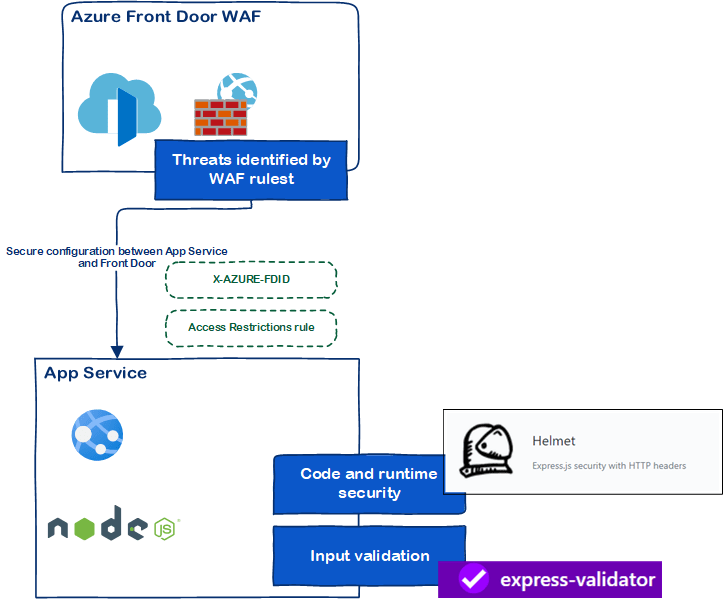
I’ve been recently playing around with Azure Front Door, and it’s WAF Policies. Here are some notes I decided to share about the my experiences mainly about securing the app from invalid and malicious inputs using Azure WAF and ExpressJS middlewares
Microsoft Azure WAF and NodeJS input checking notes
Security Checklist example
This is just a short example of items that are covered in this deployment.
- Items like pipeline security, tooling for code security, security center alerts, connecting to table storage and key vault securely, Azure Table Storage input hashing etc are enough for few more blogs 🙂
- This blog could’ve been much longer, but I wanted keep relatively straight to point, and narrow it down to securing the app from malicious inputs.
| Threat | Mitigation |
|---|---|
| OWASP top 10 mapping | Azure Front Door with WAF in prevention mode, Runtime & code security Azure Architecture, Logs testing with OWASP ZAP Zed Attack Proxy |
| Business logic | code security input validation express-validator (express-validator.github.io)Helmet (helmetjs.github.io) |
| Security Misconfigurations in Cloud Service (overlaps partially with OWASP Top10) | Azure Secure Devops Kit, Azure Security Benchmark, CIS (not covered in this blog) – And generally Azure Security Resources App service ’Access Restrictions’ rule, App Service Logs Azure Front Door Spoofing Prevention Documentation (MD files, not covered in this blog) |
Security Testing based on the checklist
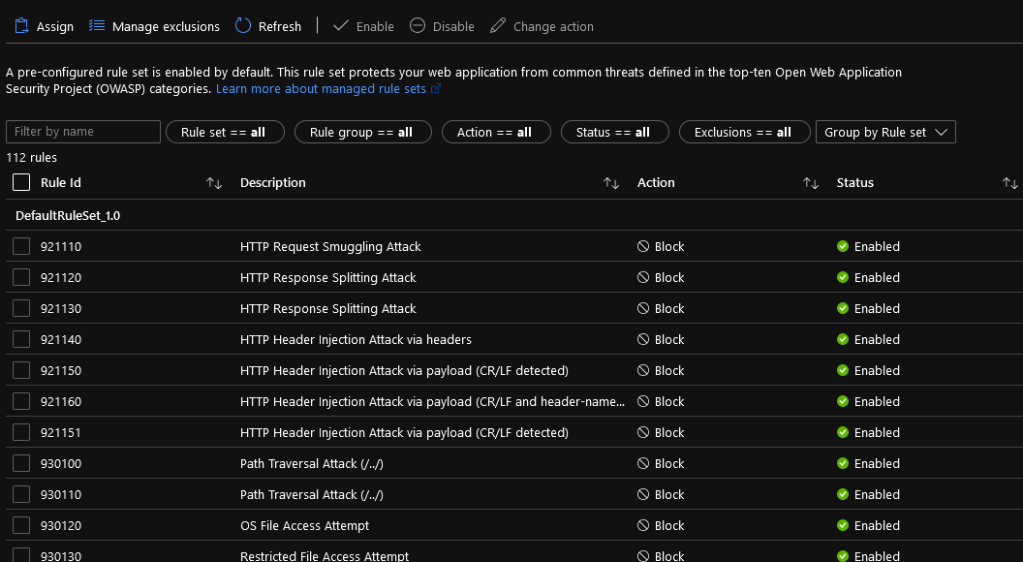
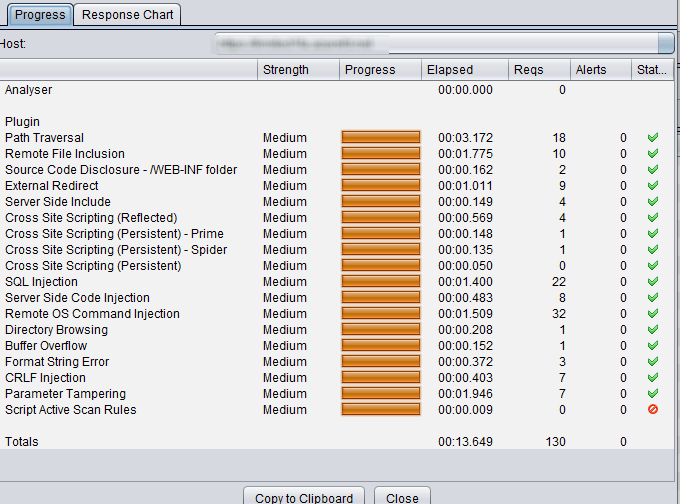
WAF basic ruleset
- Some exclusion rules also apply to allow certain characters in payloads
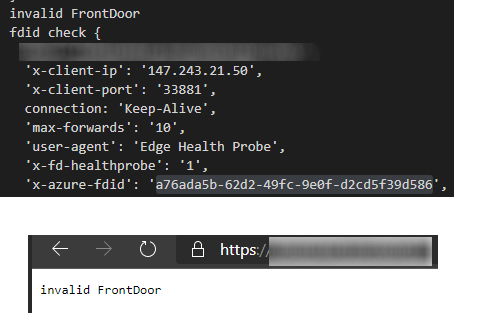
Testing Azure Front Door FDID can’t be spoofed and App Service limits traffic to Azure Front Door
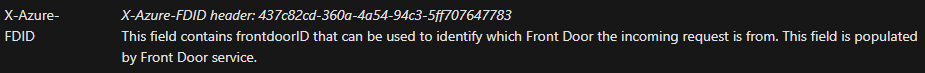
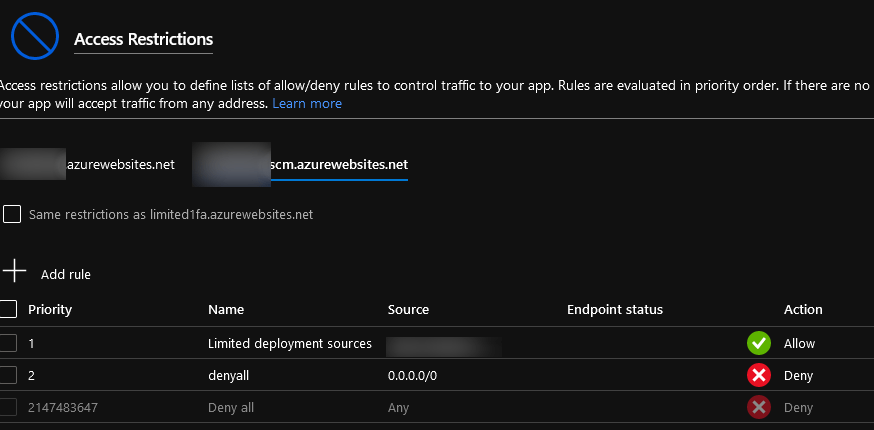
Besides limiting the traffic towards the web-app to be only allowed from Globally Azure Front Doors (Access Restrictions), its important to ensure, that the immutable identification (x-azure-fdid) security header is checked in the application middleware.
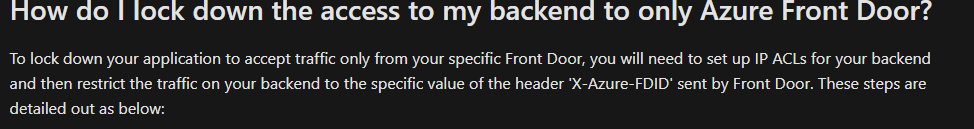
- App Service supports listing Azure Front Door as allowed source in ’Access Restrictions’
- Azure Front Door sends a header identifying the Azure Front Door Instance configured. This header is immutable, and cant be manipulated directly when Front Door Connects directly to the app service
- This is based on assumption that access restrictions are placed on L7 ’Access Restrictions’ rules, and the NodeJS implements header checking for the particular value
- Ensured that user cant supply FDID header from client-side, and if attacker deploys their own Azure Front Door against your app service instance
Access Restrictions
- Front door backend
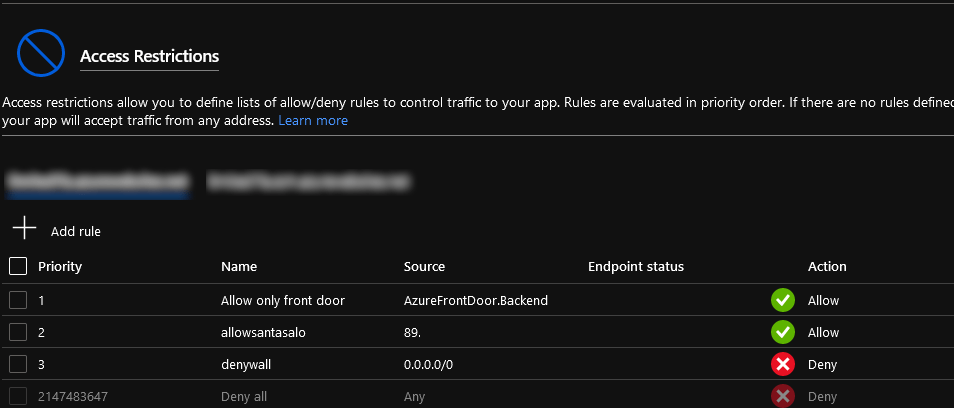
- Limiting admin and deployment access to KUDU SCM endpoints
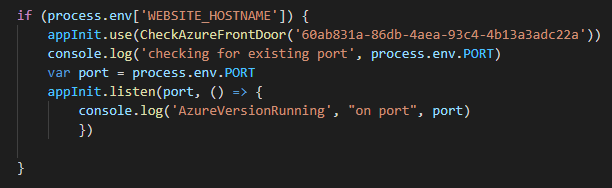
ExpressJS middlware checking for the header used when the platform is app service.
- The immutable value ’x-azure-fdid’: ’60ab831a-86db-4aea-93c4-4b13a3adc22a’,
module.exports= function (req, res, next) {
console.log('fdid check',req.headers)
if (req.headers['x-azure-fdid'] !== "60ab831a-86db-4aea-93c4-4b13a3adc22a") return next('invalid FrontDoor')
next()
}
// or
function CheckAzureFrontDoor(fdid) {
return function (req, res, next) {
console.log('fdid check',req.headers)
if (req.headers['x-azure-fdid'] !== fdid) return next('invalid FrontDoor')
next()
}
}
module.exports={CheckAzureFrontDoor}
Owasp ZAP listing of tested methods
Recommended reading
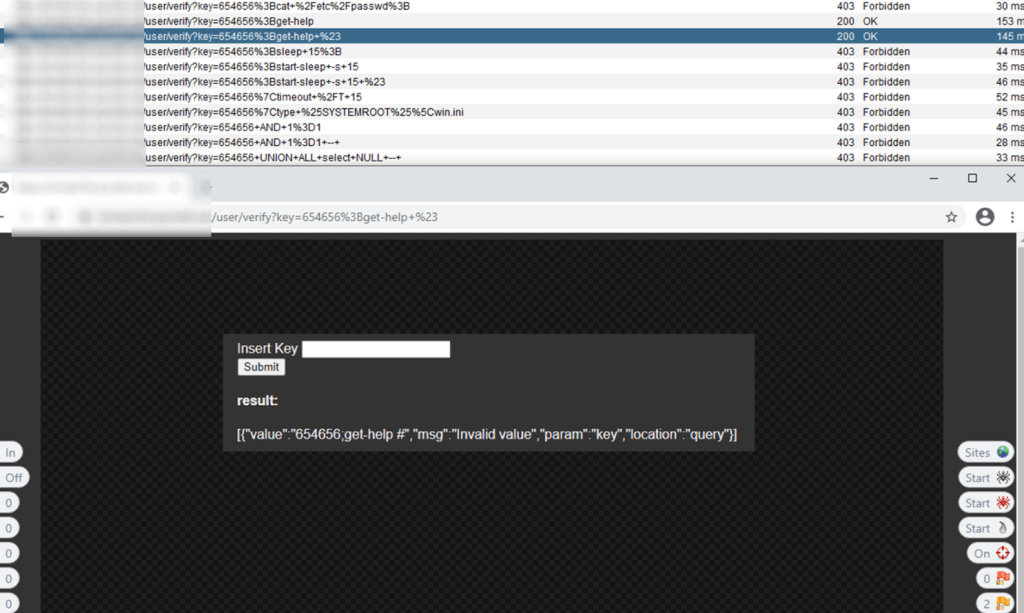
Example of tests run against the App Service protected by front door
Express validation and authorization middlewares
- Express middleware working to block request that are not in WAF’s scope
After Azure Front Door WAF, there is additional layer in the application itself.
- The NodeJS app uses additional validation in the API’s it provides for mainly for following reasons:
- Validate tokens, and bind tokens user context to limit searches into Azure Table Storage
- Tell users about whats expected in the input, in case of invalid input
- Clean up input used for Azure Graph API and Azure Table Storage
- Attempts to take care of certain inputs that don’t validate in the middleware but we’re passed from the WAF
checkBodyAndQuery('user').trim().isEmail()
checkBodyAndQuery('key').trim().isNumeric()
- User provided keys are checked to match the userObjectID in validated token, and database entry before key can be claimed.
usrvariable is only available in the back-end, based on the incoming token
var result = await findEntry(usr, await genpassHSH(req.query.key).catch((error) => {
r = error
console.log('errpr',error)
})
if (!result) {
return res.render('display',{
title: process.env.title,
userview: true,
error: r
})
}
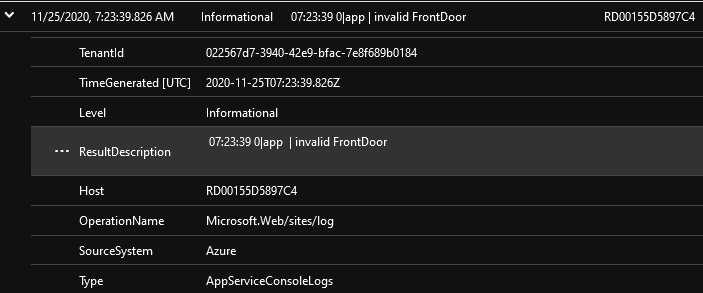
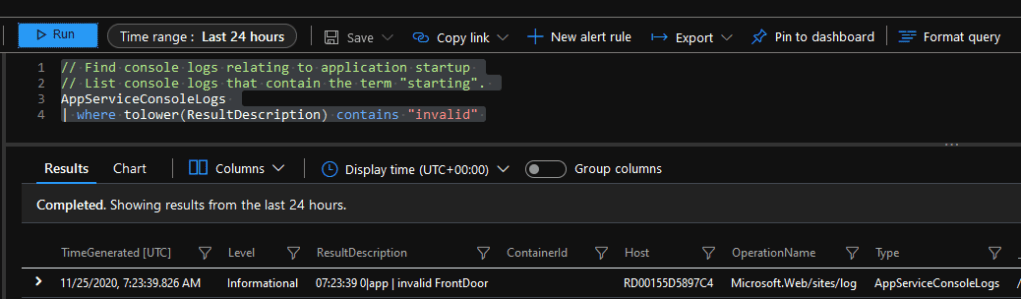
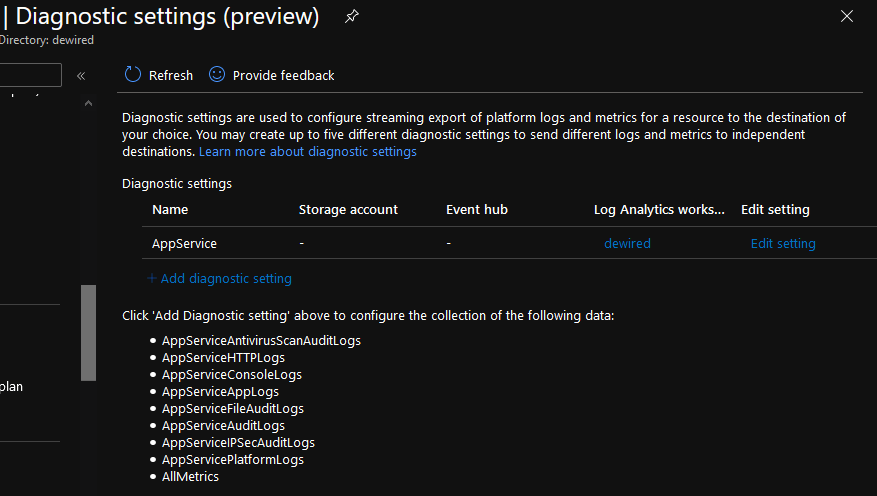
App Service Logs
- The easy way is to use exporting of AppServiceConsoleLogs to Log Analytics
- More precise way NodeJS Logging integration with Azure Log Analytics/Sentinel or Post: Create Logic App for Azure Sentinel/Log Analytics – SecureCloudBlog
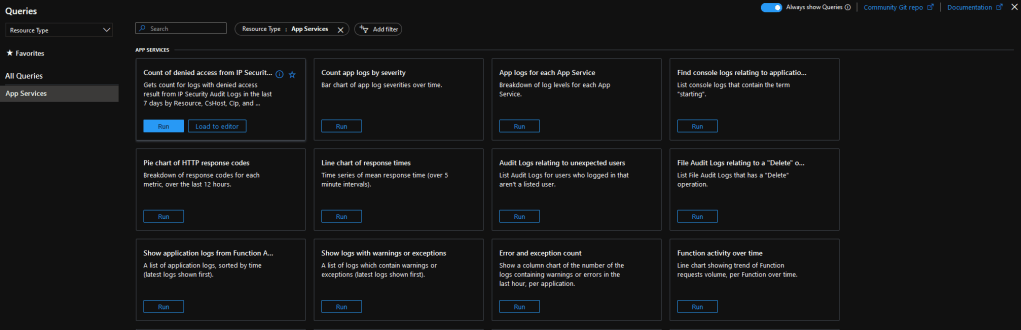
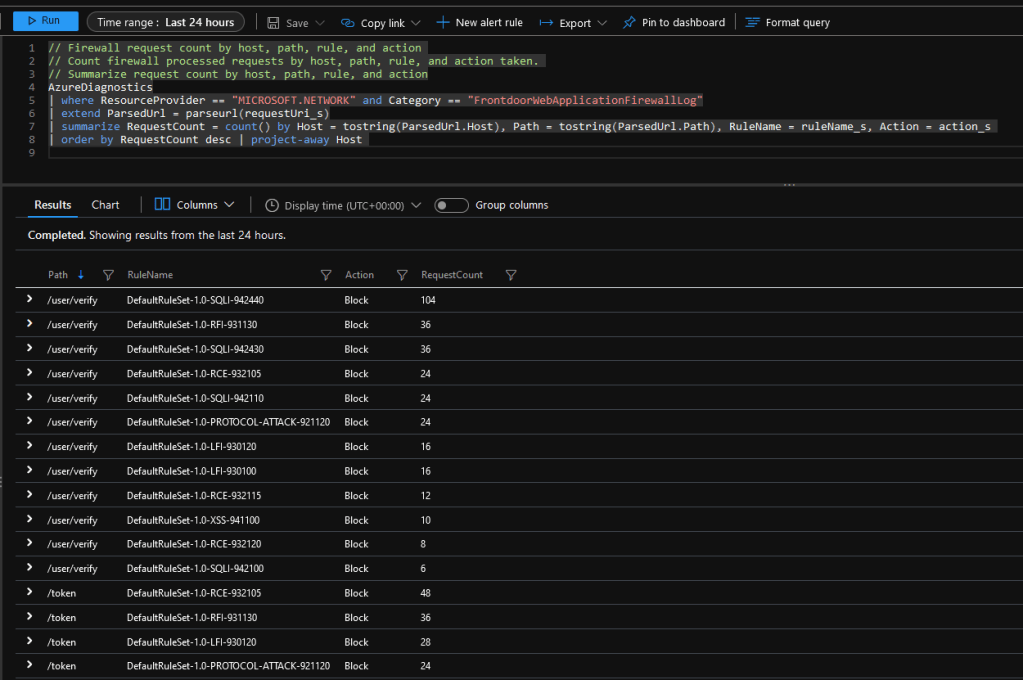
Azure Front Door WAF Logs
- WAF logs in Azure Front Door
Ending words
Azure App Service, and surrounding Azure Ecosystem offers full toolkit to monitor, and secure solutions for the whole lifecycle of any web application pretty nicely.
As stated before: This blog could’ve been much longer, but I wanted keep relatively straight to point, and narrow it down to securing the app from malicious inputs
Some further reading:
Azure Security Center Exhibits from the field – Detecting SQL Injection with Advanced Data Security
Azure Security Center – Exhibits from the field
TOP3 Picks from Azure Security Center Standard
App Service – Key Vault Vnet Service Endpoint access options explored + NodeJS runtime examples
Br Joosua!
0 comments on “Defence in depth: Securing Azure App Service with Azure Front Door WAF, NodeJS runtime Security enhancements tested with OWASP ZAP”