Few days ago a customer told me about challenges of doing secure MFA enrollment in larger enterprises. They are utilizing Azure AD Premium and using Conditional Access to block un trusted context for ‘MFA enrollment’ – This has presented interesting challenge to on boarding processes, due to the fact that employees/contractors (which have possibility of remote working) don’t go to sites that often these days. (Sites can sometimes be considered as trusted locations for MFA enrollment)
There are multiple approaches to how to solve this problem (Azure Identity Governance being one for P2 utilizing customers) Our discussion continued, and the Customer pitched an interesting idea, could there be one-time code pre -delivered to the end user, to allow limited time enrollment?
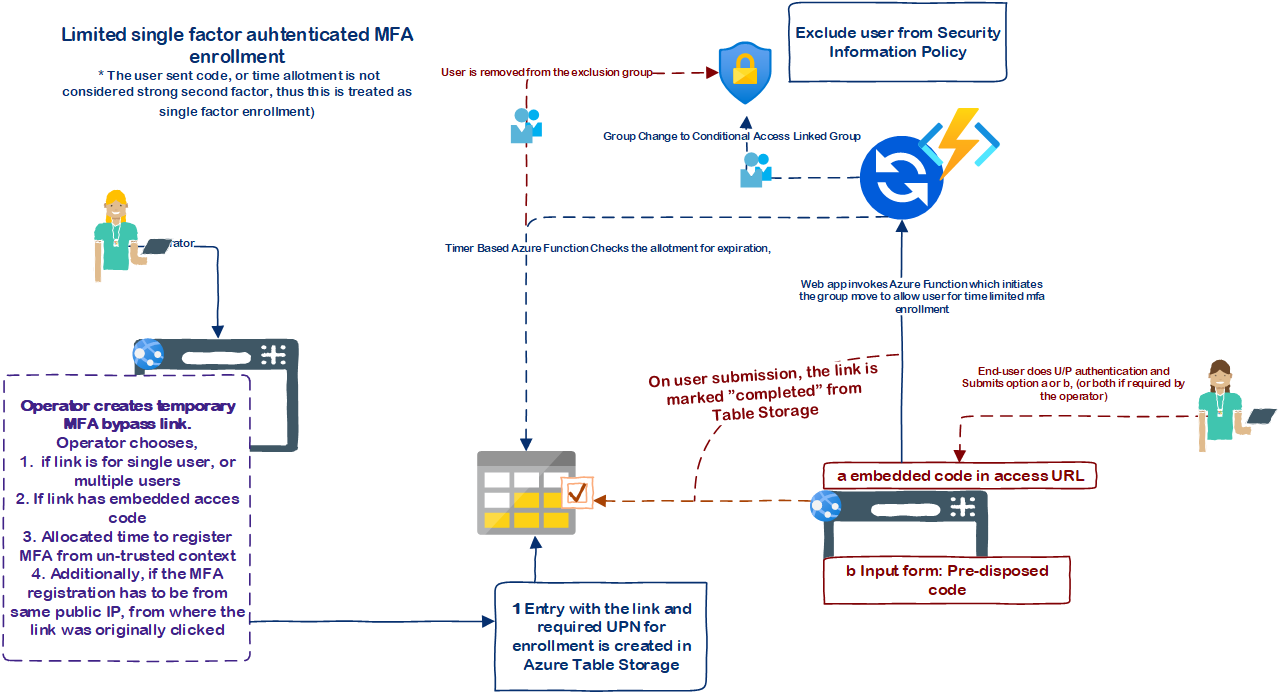
I thought about it for a moment, and understood that its fairly simple to do by controlling group membership, where the groups is added as exception to the policy. In the end let automation remove the user from the group once the allotted time has passed.
POC Solution demo

- Admin creates exemption code, which runs automation to add user for exception group
- Once user authenticates and redeems the code at the application user is placed to exemption group for the configured time
- Once the configured time has passed user is removed by the automation from the group
The solution

The solution is based on Conditional Access requiring the MFA enrollment, based on grant conditions configured for all/or individual apps.
If you’ve forced the registering of security information for all first-time signin users, regardless if the app requires MFA, then this solution will not work (Unless you place the app on another tenant, and onboard the user there with external identities, as policies are enforced per resource tenant)
- NodeJS app (Web app, and timer based function)
- The app can only add and remove the users from single group
- The app is itself excluded from Conditional Access Policies for tenant users (as its meant to allow single factor authentication to claim the one-time registration code for MFA registration)
The solution in action
This was the initial poc post, might add some updates here later, but just wanted to quickly document it
Br Joosua!

0 comments on “Covid19 Challenges for the remote enterprise: Allowing exceptions to Secure MFA enrollment”