The change from 1:5 ratio, to monthly active users
50 000 Monthly Active Users… Free of charge. When this info was initially released I had to read the announcement like 20 times – Just to make sure I am not missing any catch. This folks, as they say, is nearest thing to a ”free lunch”
- Recently pricing and branding change was introduced, to make Azure AD collaboration even more enticing, I am covering this feature in short blog post, and a some debugging I did when enabling the this feature

Background
If you want to generally learn more about Azure AD collaboration, start from here. This blog from here on is dedicated to the subject of switching the pricing model the B2B collaboration defaults to.
Configuring Azure AD for Monthly Active Users
I decided to take this feature for a spin, but faced a small bug. I am not entirely sure you will be encountering the same bug, Nonetheless, if you are testing this feature, you might need to do some fiddling, or adjust your Azure Policies.
- If you are familiar with linking Azure Subscription to B2C, you will find this some what similar to linking B2C directory to Azure Subscription
Disclaimer (Test major changes to features always in test tenant, always follow official recommendation before doing anything like this in production)
Assuming that this is already fixed, then this is the article which you should use https://docs.microsoft.com/en-us/azure/active-directory/external-identities/external-identities-pricing#link-your-azure-ad-tenant-to-a-subscription
Debug findings
I had these findings collected from two different tenants, on of the tenants is my honeypot tenant dewired.onmicrosoft.com
- If you have Azure Policy Enabled for the tenant, the Policy might prevent you from deploying the feature. Adjust the policy so, that you can deploy the feature

List of available regions for the resource type is 'global,
unitedstates,europe,asiapacific'."}}
Resource 'dewired.onmicrosoft.com' was disallowed by policy. Policy identifiers: '[{"policyAssignment":{"name":"Allowed locations","id":"/providers/Microsoft.Management/managementGroups/ENTP-MG-ROOT/providers/Microsoft.Authorization/policyAssignments/6f6a4c83de3e4d05b632762a"},"policyDefinition":{"name":"Allowed locations","id":"/providers/Microsoft.Authorization/policyDefinitions/e56962a6-4747-49cd-b67b-bf8b01975c4c"}}]'.
2. If you don’t have policy for Azure enabled, but your tenant is in Europe, with specific location such as ”Finland” set in initial creation of the Azure AD

The provided location 'Finland' is not available for resource type 'Microsoft.AzureActiveDirectory/guestUsages'. List of available regions for the resource type is 'global,unitedstates,europe,asiapacific'. or Cannot create resource with location: 'United States'. Please use location: 'Europe' to create resource for b2c directory: '.onmicrosoft.com'.
3. This is unlikely error, but for some reason the subscription didn’t have resource provider for AAD enabled (The fix is to add the resource provider in subscription settings)

The subscription is not registered to use namespace 'Microsoft.AzureActiveDirectory'. See https://aka.ms/rps-not-found for how to register subscriptions.

- Now at this point you should be able to link the subscription

Still not?
You might have a situation where the GUI is not using the location of your tenant to create the tenant. In this case I resolved this by modifying the payload browser is making in PowerShell
- Use CHREDGE or CHROME
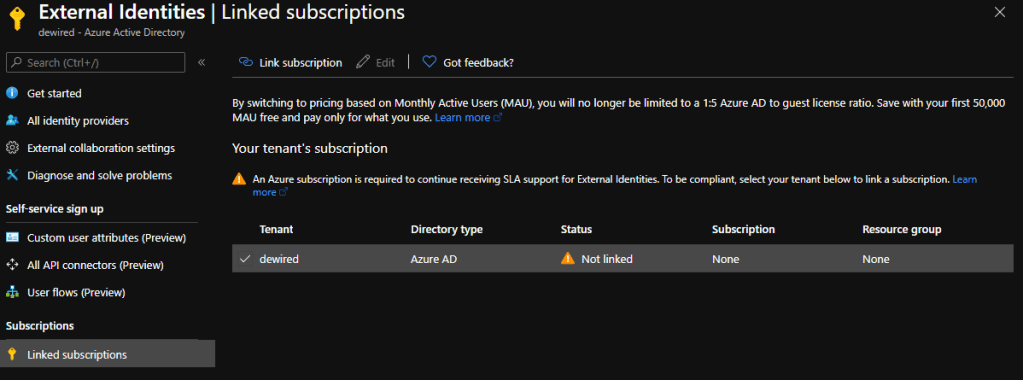
- From portal select External Identities
- Most of the B2B collaboration settings are these days under ”External Identities”

- From there we choose the ’Linked subscriptions’

- Now at this point use the developer mode to capture the failing request to powershell by clicking ’apply’ in the link subscription dialog. Now you might get two different errors.
- Ensure that the location is one of the supported locations ( in my case Azure AD setting was created with Finland, so mine is Europe)
List of available regions for the resource type is 'global, unitedstates,europe,asiapacific'."}}
In the call change the location to match one these locations, and run the call in PS. The PS should call in non -error HTTP status code
Invoke-WebRequest -Uri "https://management.azure.com/subscriptions/3539c2a2-cd25-48c6-b295-14e59334ef1c/resourceGroups/RG-B2XMAU/providers/Microsoft.AzureActiveDirectory/guestUsages/dewired.onmicrosoft.com?api-version=2020-05-01-preview" `
-Method "PUT" `
-Headers @{redacted} `
-ContentType "application/json" `
-Body "{`"id`":`"/subscriptions/3539c2a2-cd25-48c6-b295-14e59334ef1c/resourceGroups/RG-B2XMAU/providers/Microsoft.AzureActiveDirectory/guestUsages/dewired.onmicrosoft.com`",`"name`":`"dewired.onmicrosoft.com`",`"location`":`"Europe`",`"tags`":{},`"type`":`"Microsoft.AzureActiveDirectory/GuestUsages`",`"properties`":{`"tenantId`":`"46d2c4e6-a732-4fb4-b9f8-374af03f3f58`"}}"
Till next time!
Br, Joosua
0 comments on “Debugging the switch to Monthly Active Users in Azure AD B2X Collaboration”