I was recently working with community members to test mapping of tactics and techniques to events in Azure Sentinel created via analytics.
I only created this post and query as quick documentation without any further background: Since I did not find documentation of the data formats used to create these on a quick browse:
- The purpose of query is to demonstrate the correct format for mapping tactics and techniques, rather than to detect specific threats
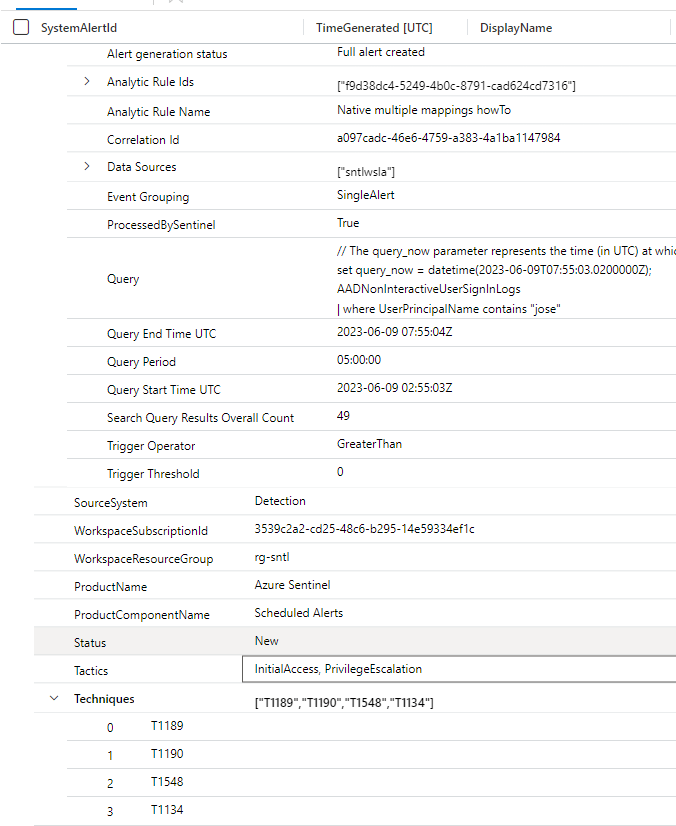
In order to understand how Microsoft maps these for the T&T’s selected from the analytics rule wizard, I checked one of the incidents created from the analytics rule
Tactics is a single string
Techniques is a stringified array
Mapping to custom event
Please note, this event does not have any particular logic, the main purpose is to highlight the correct format for surfacing these events in incidents: If you plan to use these, store the mappings to Github for example, and fetch them via externalData(), and then add whatever logic you desire to have for the incident.
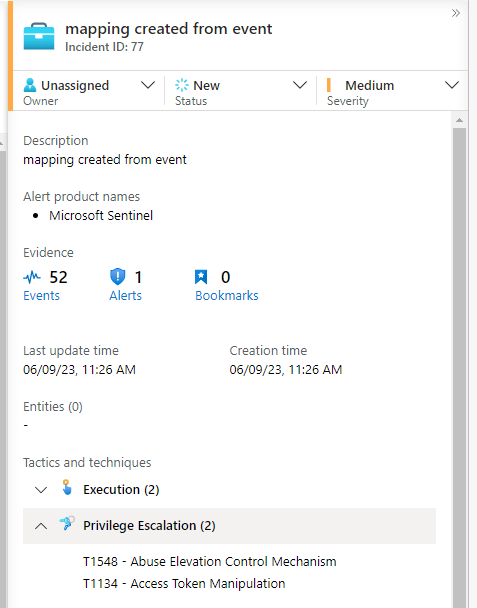
Bogus incident
This incident highlights the mappings in GUI, which was the original aim of this experiment
Below the bogus query in the analytics rule
- I used the dynamic() casting just to have more comfortable/readable way to insert technique values into stringified array
AADNonInteractiveUserSignInLogs
| where UserPrincipalName contains "jose"
| extend tacticsMap = "Execution,PrivilegeEscalation"
| extend techMap = tostring(dynamic(["T1059","T1609","T1134","T1548"]))
Mapping for the query

End of post
See following references for official documentation https://learn.microsoft.com/en-us/azure/sentinel/detect-threats-custom#analytics-rule-wizardgeneral-tab

0 comments on “Microsoft Sentinel – Experimenting with Tactics and Techniques mapping from events to incidents via Analytics rules”