Most typical reason I see that the SCM endpoint is not secured on App Services is that these apps are often updated by MS hosted Azure DevOps agents.
Luckily you can increase the security of your app service greatly – If you previously did not have any network restrictions on SCM endpoint, you can now have the SCM endpoint restricted to ’Azure Cloud’ – Yes that is still lot of attack surface, but is exponentially less than the whole internet being able to probe your App Service.
Setup
Example pipeline below using Service Connection with Client Credentials (certificate)
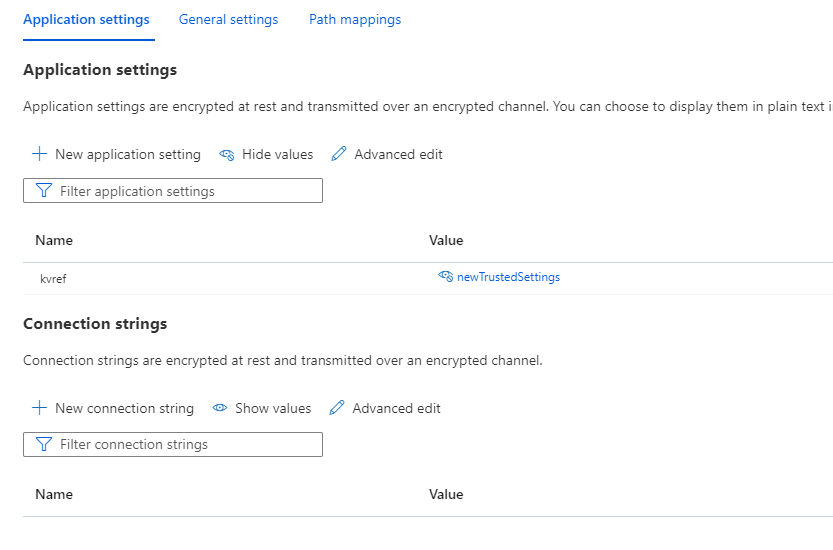
- Pipeline updates app setting for network restricted web app

- Setting is updated as follows to app service

- Network restrictions uses the ’tag’ setting for ’Azure Cloud’

End of post

0 comments on “Azure Devops – Update network restricted App Service via Microsoft-hosted Azure DevOps agent”