I am not certain for how long there has been possibility of configuring logic apps to use managed identity for calling functions, so I created this short post to document the steps.
Background
There is excellent article at @docs outlining the managed identity option for calling upstream services from Logic Apps

Guide
The steps are very simple
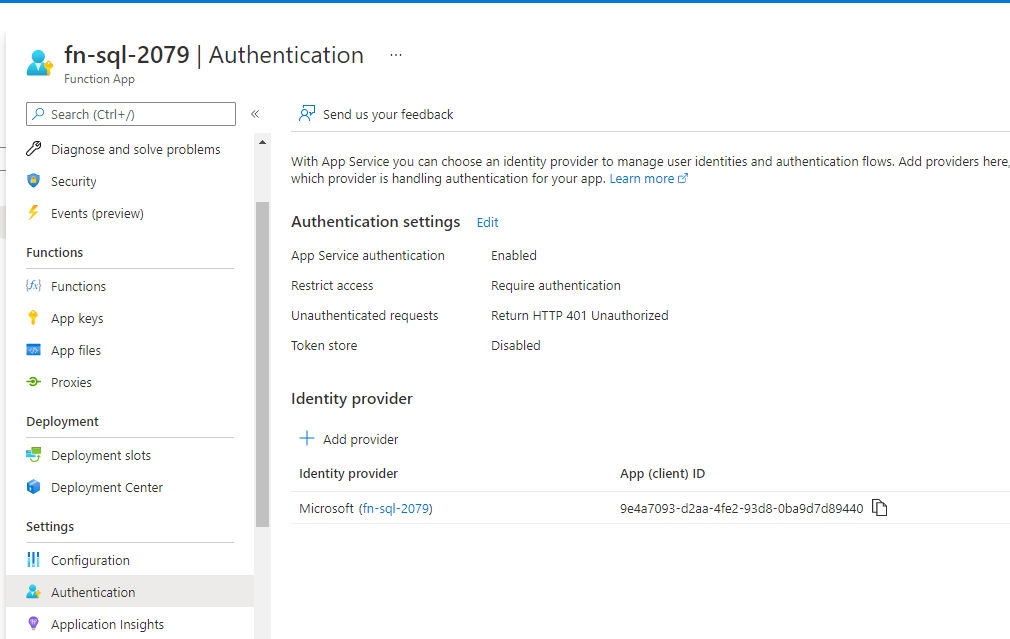
- Enable your function for authentication
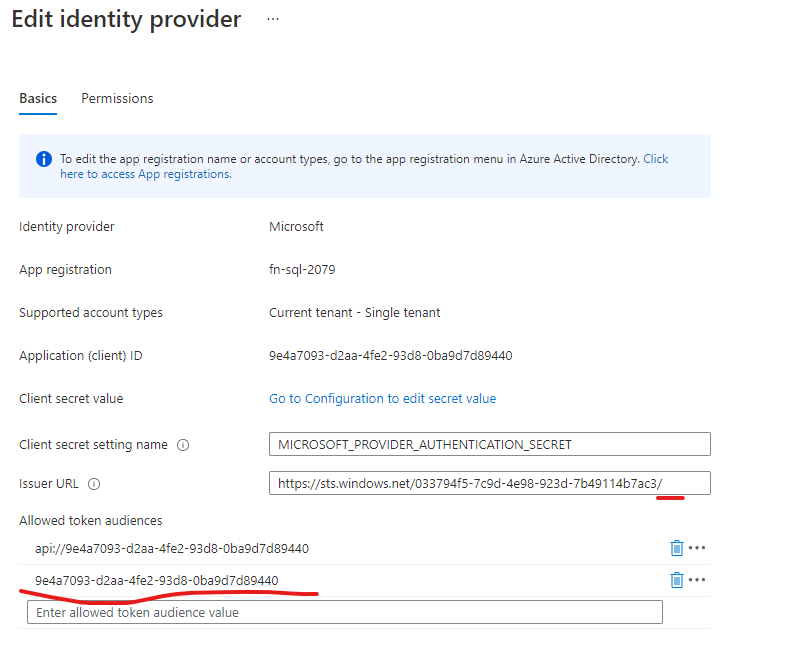
- Ensure you allow audience of the appid, and v1 endpoint to be the issuer (remove v2.0 from issuer, unless you are forcing logic app to use v2 endpoint with HTTP request version)
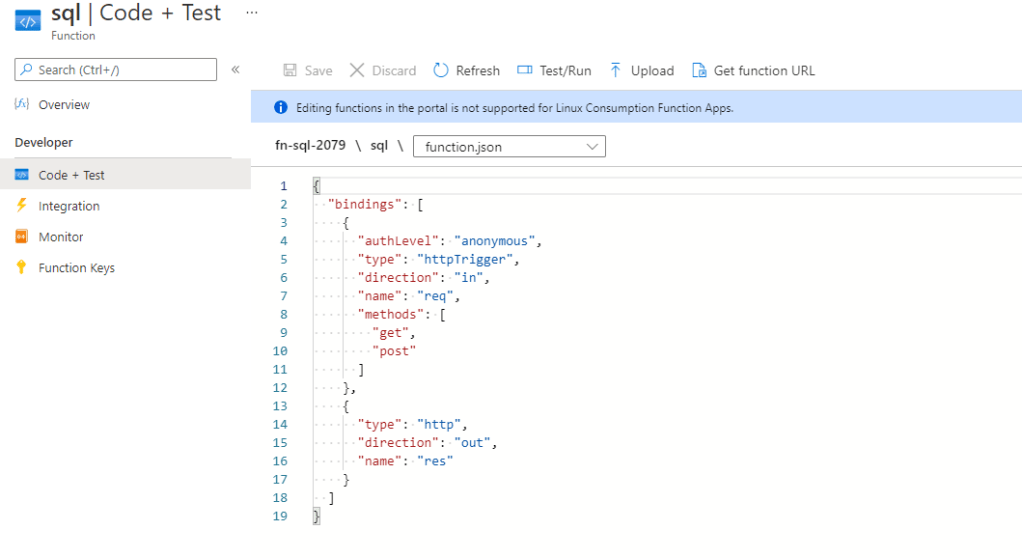
- If you have existing function change (after enabling authentication) ”authLevel” to anonymous (note. this only removes the function level
?code=""authentication, function is now authenticated by Azure AD, as are the rest of the functions)
{
"bindings": [
{
"authLevel": "anonymous",
"type": "httpTrigger",
"direction": "in",
"name": "req",
"methods": [
"get",
"post"
]
},
{
"type": "http",
"direction": "out",
"name": "res"
}
]
}
- You can try the ”upload” dialog for function.json, if you don’t have automated deployment configured for the function
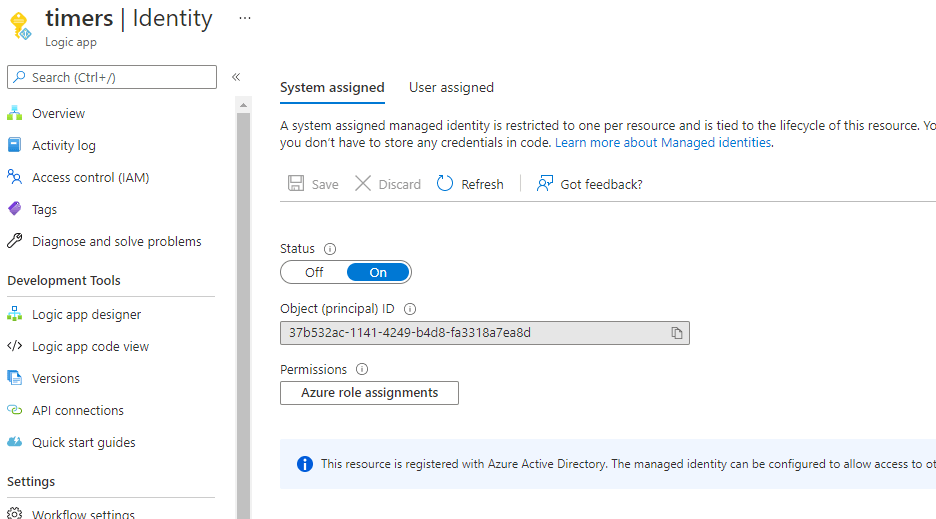
- Enable managed identity in your logic app
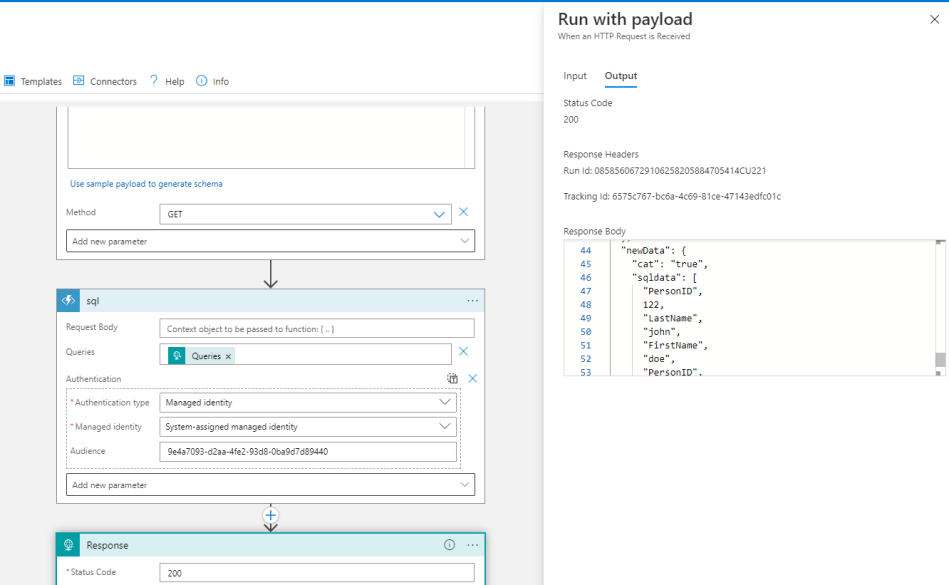
- Create the function step in Logic App


"sql": {
"inputs": {
"authentication": {
"audience": "9e4a7093-d2aa-4fe2-93d8-0ba9d7d89440",
"type": "ManagedServiceIdentity"
},
"function": {
"id": "/subscriptions/6193053b-408b-44d0-b20f-4e29b9b67394/resourceGroups/RG-FN-2079/providers/Microsoft.Web/sites/fn-sql-2079/functions/sql"
},
"queries": "@triggerOutputs()['queries']"
},
"runAfter": {},
"type": "Function"
}
- Now call your Logic App to test that the authorization works

Troubleshooting
Both of these errors can arise, if you have not configured settings as configured in the outlined step
BadRequest. Http request failed as there is an error getting AD OAuth token: 'AADSTS500011: The resource principal named api://9e4a7093-d2aa-4fe2-93d8-0ba9d7d89440/.default was not found in the tenant named flex
{
"code": 401,
"message": "IDX10205: Issuer validation failed. Issuer: '[PII is hidden. For more details, see https://aka.ms/IdentityModel/PII.]'. Did not match: validationParameters.ValidIssuer: '[PII is hidden. For more details, see https://aka.ms/IdentityModel/PII.]' or validationParameters.ValidIssuers: '[PII is hidden. For more details, see https://aka.ms/IdentityModel/PII.]'."
}
Recommended reading
Hardening app registrations, especially for managed identities (Client Credentials) https://github.com/jsa2/aadClientCredentialsDoc#checklist
0 comments on “Authorize Logic Apps in Azure Functions with Logic App managed identity and Azure AD”