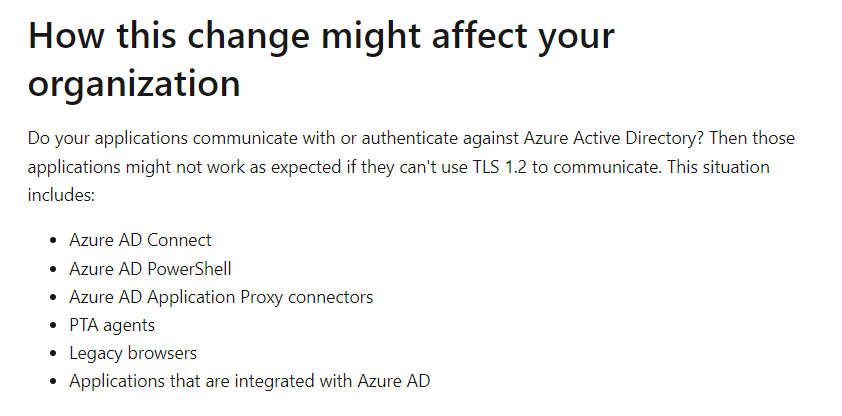
Azure AD will stop supporting sub TLS 1.2 versions, so you might want to investigate whether you have clients that are going to be impacted by the deprecation.
The deprecation date is mentioned on the links below (January 31st, 2022, at the time of writing)
Background
There is good guidance available here on these two articles
Act fast to secure your infrastructure by moving to TLS 1.2!
Enable support for TLS 1.2 in your environment for Azure AD TLS 1.1 and 1.0 deprecation
Typical use cases are also mentioned in the articles
Investigation using Azure Monitor
If you have both sources exported from Azure AD you can use query below
union SigninLogs, AADNonInteractiveUserSignInLogs
| where TimeGenerated > now() -30d
| project AuthenticationProcessingDetails, UserPrincipalName, IPAddress, UserAgent, AppDisplayName, ClientAppUsed
| mv-expand parse_json(AuthenticationProcessingDetails)
| where AuthenticationProcessingDetails.key == "Legacy TLS (TLS 1.0, 1.2, 3DES)" and AuthenticationProcessingDetails.value == "True"
| summarize count() by UserPrincipalName, ClientAppUsed, AppDisplayName, UserAgent, tostring(AuthenticationProcessingDetails)
| summarize make_set(strcat(count_, ':', ClientAppUsed, ':' ,AppDisplayName )) by UserPrincipalName, AuthenticationProcessingDetails
The query displays count and client details

0 comments on “Azure AD deprecation of TLS 1.0 and 1.1 – how to investigate using Azure Monitor?”