Many use cases of Azure Kubernetes Service are based on running an private AKS cluster that exposes services only via Web Application Firewall (such as Azure Application Gateway), or exposes services only internally.
Auditing / and or denying creation of public load balancers ensures that the governance principle for the particular AKS instance followed.
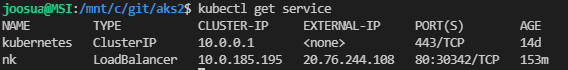
ControlId Ensure public load balancer creation is audited or denied
Exhibits

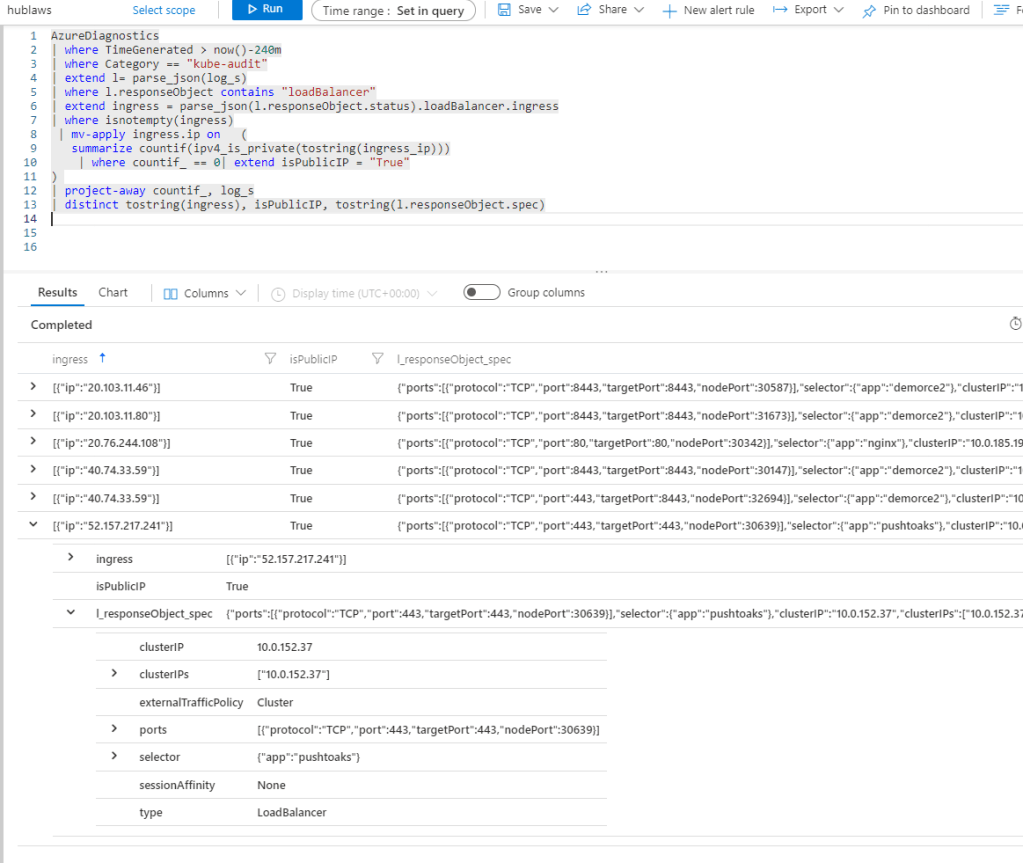
Check the control from log analytics
//adjust the time if needed
AzureDiagnostics
| where TimeGenerated > now()-240m
| where Category == "kube-audit"
| extend l= parse_json(log_s)
| where l.responseObject contains "loadBalancer"
| extend ingress = parse_json(l.responseObject.status).loadBalancer.ingress
| where isnotempty(ingress)
| mv-apply ingress.ip on (
summarize countif(ipv4_is_private(tostring(ingress_ip)))
| where countif_ == 0| extend isPublicIP = "True"
)
| project-away countif_, log_s
| distinct tostring(ingress), isPublicIP, tostring(l.responseObject.spec)
References
Source: https://aka.ms/kubepolicydoc.
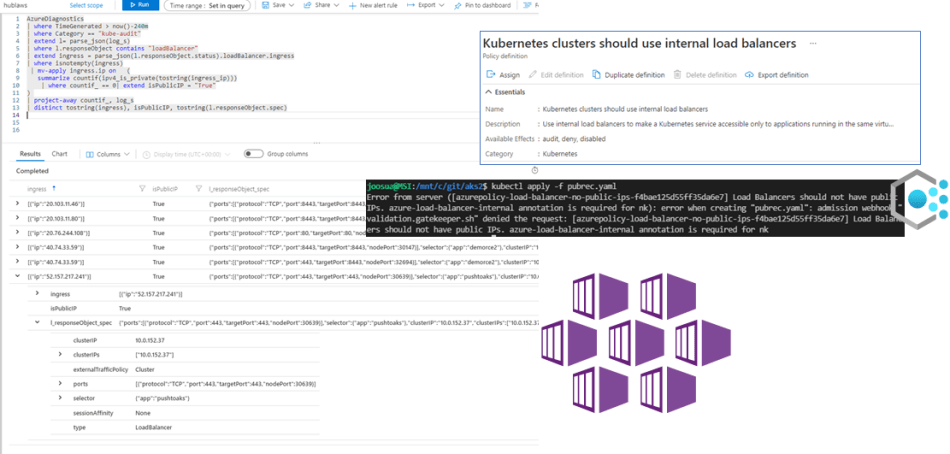
| Policy | Description |
|---|---|
| Kubernetes clusters should use internal load balancers | Use internal load balancers to make a Kubernetes service accessible only to applications running in the same virtual network as the Kubernetes cluster. For more information, see https://aka.ms/kubepolicydoc. |
Blog related to Azure Policy
KQL example
https://stackoverflow.com/questions/68564324/filter-ips-if-they-are-in-list-of-range
0 comments on “AKS – Ensure public load balancer creation is audited or denied on Azure Kubernetes”