I recently received a very interesting question: ”Can we pass the access token from DevOps Service Connection for Azure Resource Manager in our container job within the pipeline?”
The first thing that came to my mind is the system variable $(System.AccessToken)? but then I realized its only for accessing API’s of Azure DevOps (for example creation of Pull request via Azure DevOps API)
Next I checked if bash would support using the service Connection via the azureSubscription context, but that wasn’t available either. Bit after searching for the answers in the place developers go looking for them (what would we do without stack overflow… :)) I found post (1) detailing the use of AZ CLI for just the purpose.
What followed was simple a flow to achieve this
- TASK: use AzureCLI@ task to get the access token
- TASK: Call resources with you favorite language/tool (for me this is NodeJS, as I can do various other things with it) – But for any use case these could be CURL, invoke-restMethod etc
Example Use Case: Get Token for Graph API from DevOps Pipeline using the Service Connection SPN
- Create the service connection (I am using certificate based credential Azure DevOps – use certificate for Azure Service Connection SPN)
- Assign permissions to any Azure AD protected API from Azure AD management (My use is Conditional Access Management, Demo: Conditional Access Automation with Azure DevOps and Node.JS)

pipeline.yaml
trigger:
branches:
include:
- access
variables:
- name: graphApiToken
value: empty
jobs:
- job: A
pool:
vmImage: 'Ubuntu-20.04'
steps:
- checkout: self
persistCredentials: true
- task: AzureCLI@2
displayName: 'Get Graph API Access Token'
inputs:
scriptType: pscore
scriptLocation: inlineScript
azureSubscription: CertCred
addSpnToEnvironment: true
inlineScript: |
$token= & az account get-access-token --resource=https://graph.microsoft.com --query accessToken
Write-Host("##vso[task.setvariable variable=graphApiToken]$token")
- bash: node restClient.js $(graphApiToken)
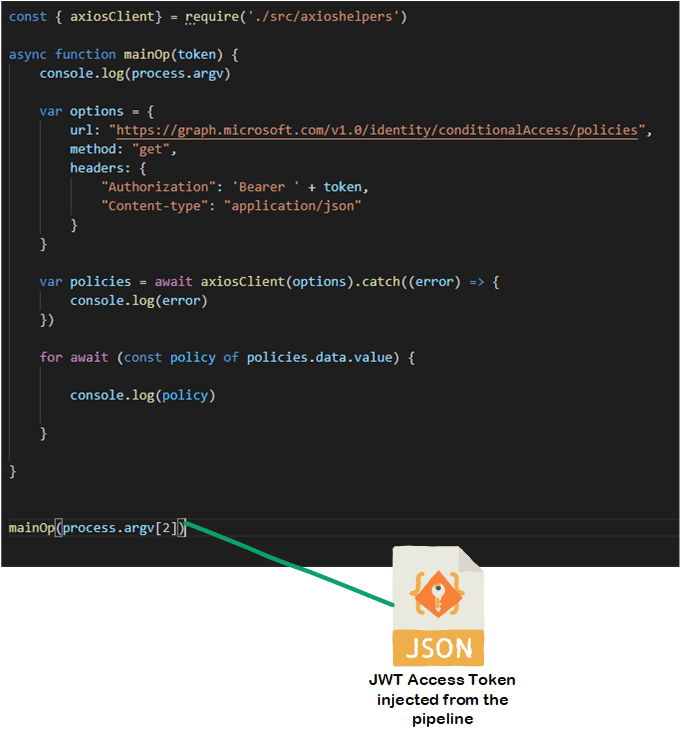
Service example using the access token
As you can see the last task ’- bash’ calls NodeJS restclient
- In the this example NodeJS get Azure AD Conditional Access Policies from Graph API
- Bear in mind, that this could be any Azure AD protected API (function, api management, you name it) which you assigned permissions for Service Connection SPN in Azure AD

Good to understand
- The main use case for this particular token is Azure Resource Manager, but in my use case (Graph API) its now in dual use, which might not always be desirable if you want to limit the scope regarding API’s for the client. But for sure, you could just use it for the first use case ”Pass the access token to another client within pipeline” – and not request permissions for another powerful API with it.
- There is some overhead invoking Azure CLI just for getting the access token, but on the other hand, this is Azure Pipeline, and not Azure Function (with latter one, the performance with cold start could be concern)

Nicely articulated! This blog indeed good in understanding how to access Azure AD-protected API from the DevOps pipeline.
TykkääTykkää
Thx!
TykkääTykkää