I was recently asked about adding Directory Schema Attribute to JWT token emitted from Azure AD. I recently wrote how to query these attributes before mapping them to SAML apps in Azure AD, but had not tested adding them to OAuth2 Access Tokens.
Guide
- First ensure that you can retrieve the attribute (further info here)
- From results take note of the attribute key:
<key> extension_47caeaeda62048129438499e0872cdb2_url <value> [ 'https://securecloud.blog', 'https://securecloud.blog/about' ],

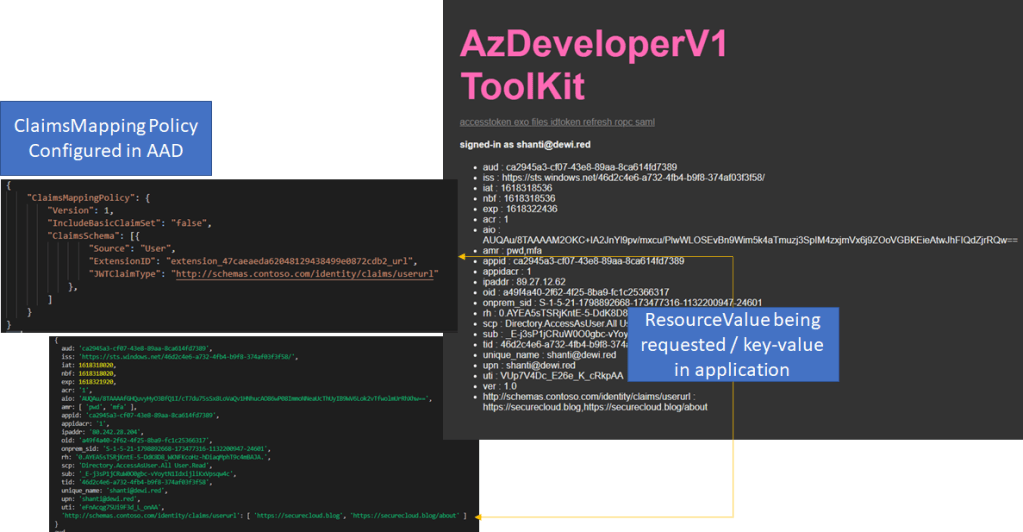
- Map the Attribute to Azure AD Policy (This requires use of AzureADPreview module)
- ExtensionID: is the full name of the key that was noted on earlier step
$policytemplate = @'
{
"ClaimsMappingPolicy": {
"Version": 1,
"IncludeBasicClaimSet": "false",
"ClaimsSchema": [{
"Source": "User",
"ExtensionID": "extension_47caeaeda62048129438499e0872cdb2_url",
"JWTClaimType": "http://schemas.contoso.com/identity/claims/userurl"
},
]
}
}
'@
$pol = New-AzureADPolicy -Definition ($policytemplate) -DisplayName ("Policy_DirectorYSchema_" + ([System.Guid]::NewGuid().guid)) -Type "ClaimsMappingPolicy" -IsOrganizationDefault $false
$spnob = Get-AzureADServicePrincipal -all $true | Out-GridView -PassThru
#$spnob select only the app you want to #modify
Add-AzureADServicePrincipalPolicy -Id $spnob.ObjectId -RefObjectId $pol.Id
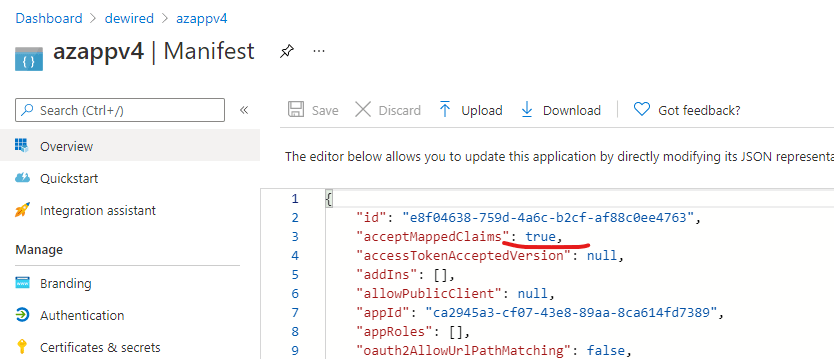
- From app manifest set ”acceptMappedClaims”
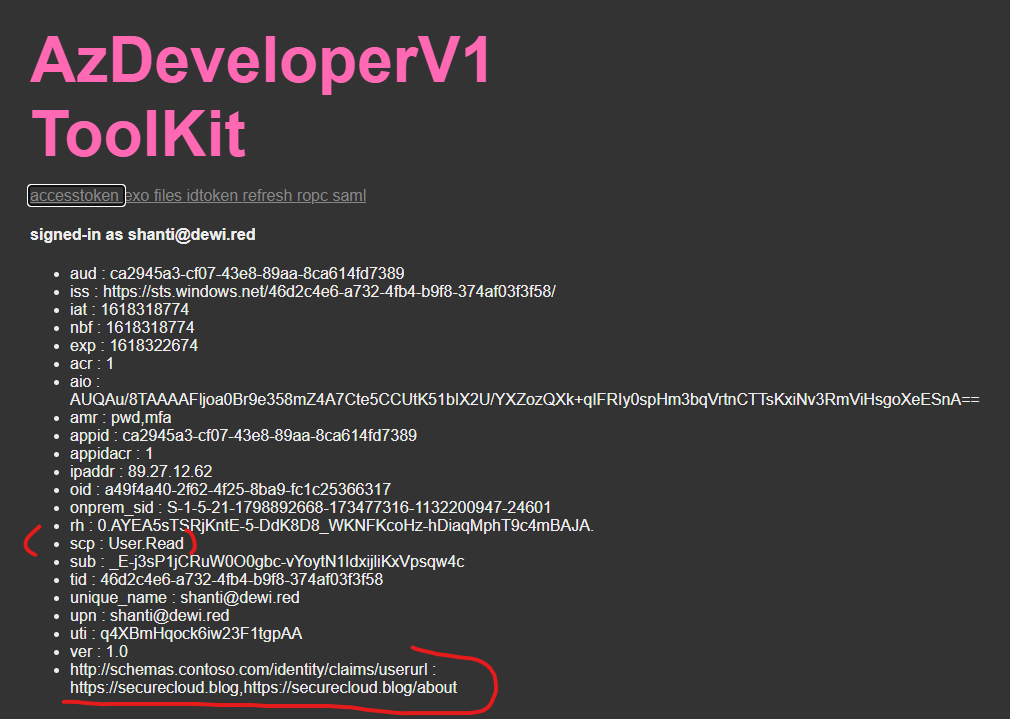
- Request access token for the app (Example of the authorization url)
https://login.microsoftonline.com/46d2c4e6-a732-4fb4-b9f8-374af03f3f58/oauth2/authorize? client_id=ca2945a3-cf07-43e8-89aa-8ca614fd7389 &redirect_uri=https://az.dewi.red/token &resource=ca2945a3-cf07-43e8-89aa-8ca614fd7389 &response_mode=query&response_type=code
- End result includes the directory schema extension value
Permissions
I did my testing with ”Access directory as the signed in user”, but less privileged permissions are likely to work too
I did test later with just user.read, but due to just writing quick blog, I did not test it again, to see if there is delay with permission propagation.
References
Use Azure AD schema extension attributes in claims – Microsoft identity platform | Microsoft Docs
0 comments on “Add Directory Extension attribute to Azure AD Access Token”