Introduction
In this blog I wanted to share Proof-Of-Concept demo of security operator receiving Teams Notifications, and then access the message for quick triaging on the security groups Team channel.
The feature is relatively simple, so I was able to craft a demo on in a breeze. The last sentence summarizes in generally what I do with Azure these days 🙂 Crafting and fine tuning different security related concepts.
I have also created a deployment guide, if you want to test this feature in test environment
PoC components
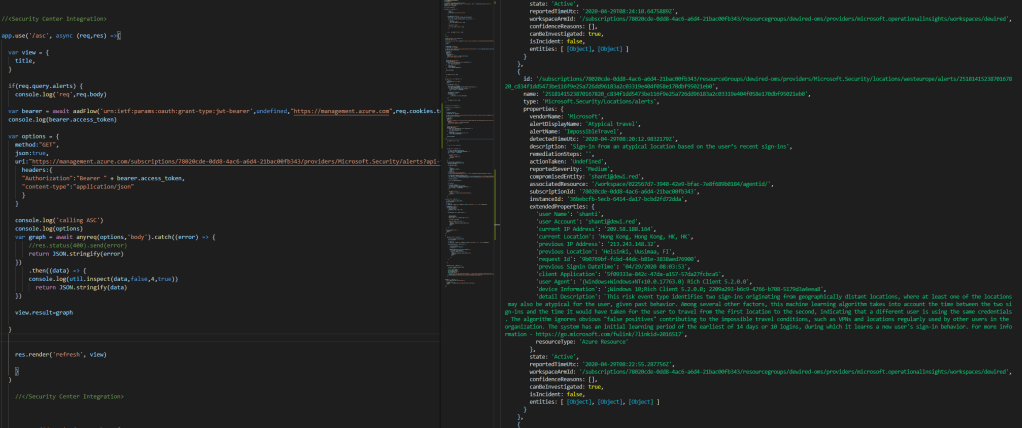
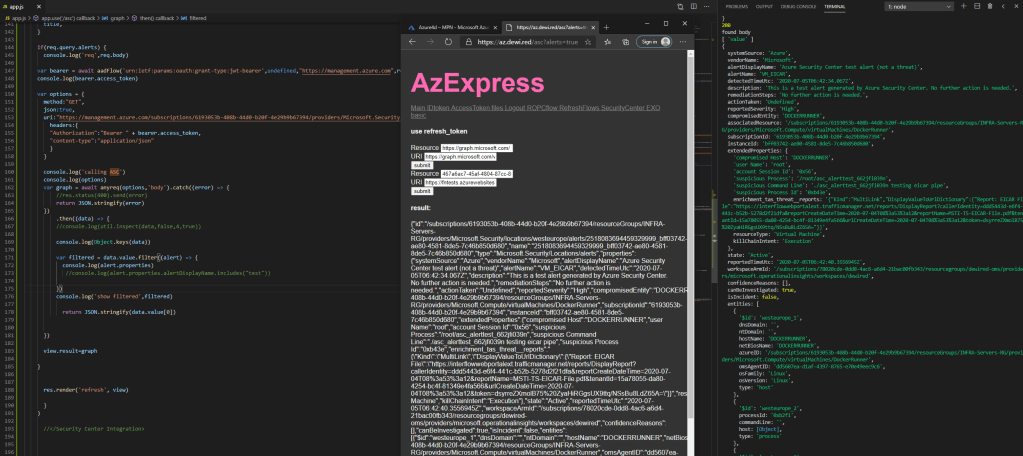
- The demo is built on NodeJS and Teams MessageCards concept and some prefetched security center events via the security center API
- Going forward one could very likely do this all also as Logic Apps, and different Sentinel Views for triaging.
- I opted for Node, because I can add small inline code chunks to achieve basically any feature with relatively low amount of effort.
PoC Video
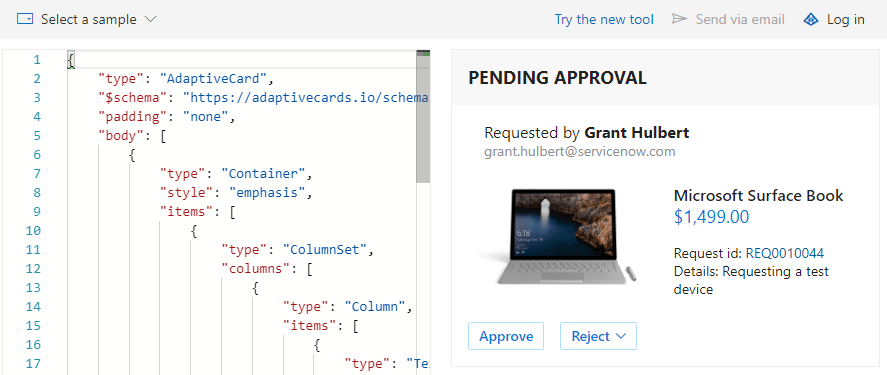
Teams MessageCards
Teams has well known framework for receiving messages via the messageCards framework. Its hard to state how powerful this framework is, but I will try to do at least some justice to it by showing simple demo.
Benefits of an example scenario?
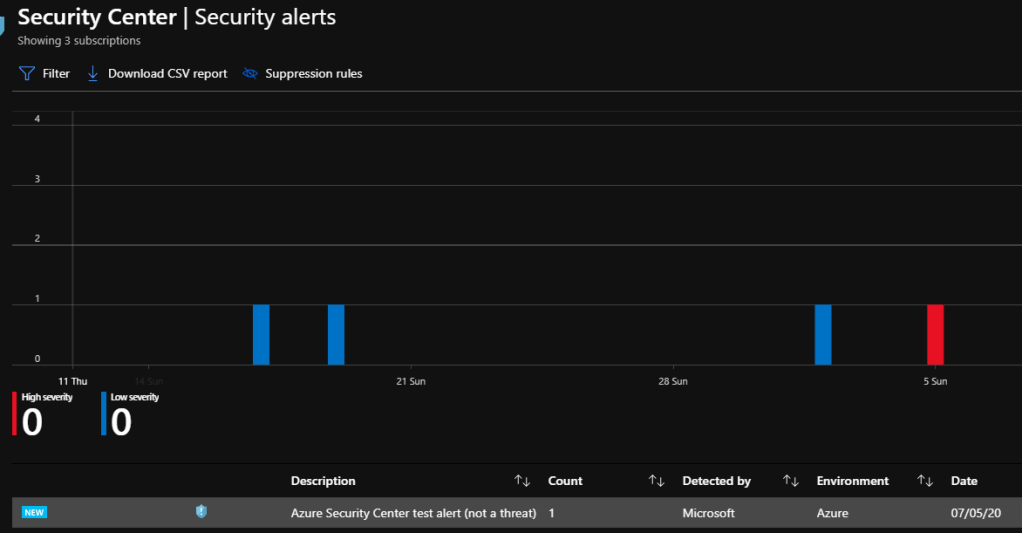
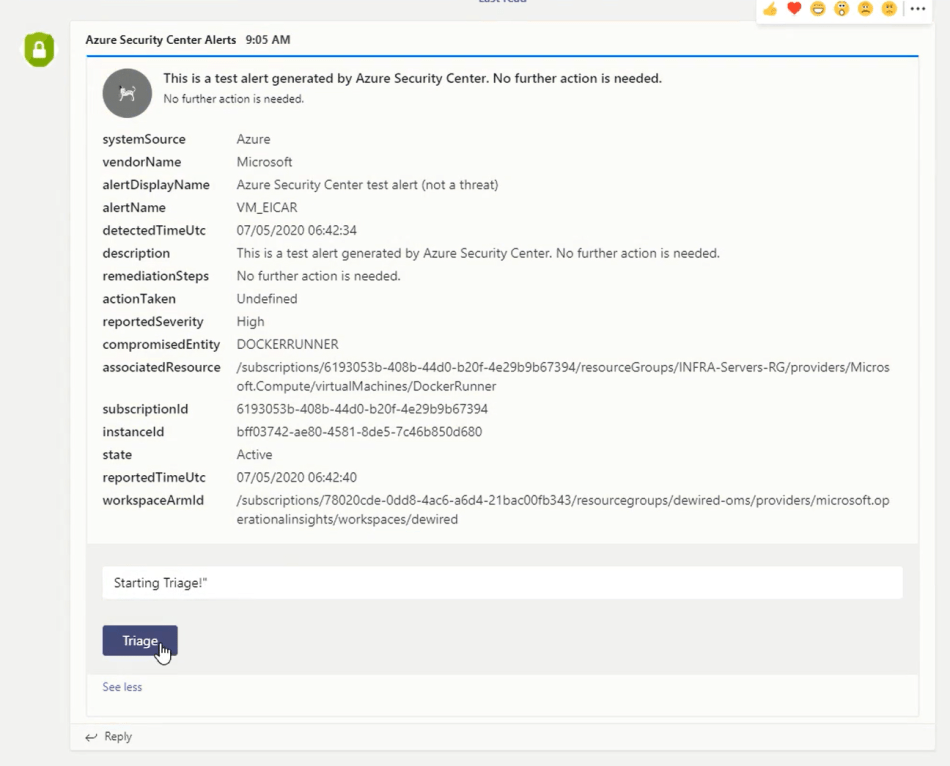
Scenario: New Security Center Alert pops up in Security Center; Event is also now visible in the Security Groups Teams channel.
Benefit: Security operators can now start triaging the event, and retain an coherent real-time messaging under the alert. Alert can be also dismissed/resolved/assigned, with justification/resolution text part.
Further background
- I am keeping the scenario fairly simple, but know that the possibilities for extending this simple concept are virtually endless, and many better examples are probably out there. If you are interested, check the ”MessageCard PlayGround”
- In this example I am using Azure Functions on next parts of the PoC (NodeJS runtime), if you are interested about Azure Functions, you could check some of my related posts
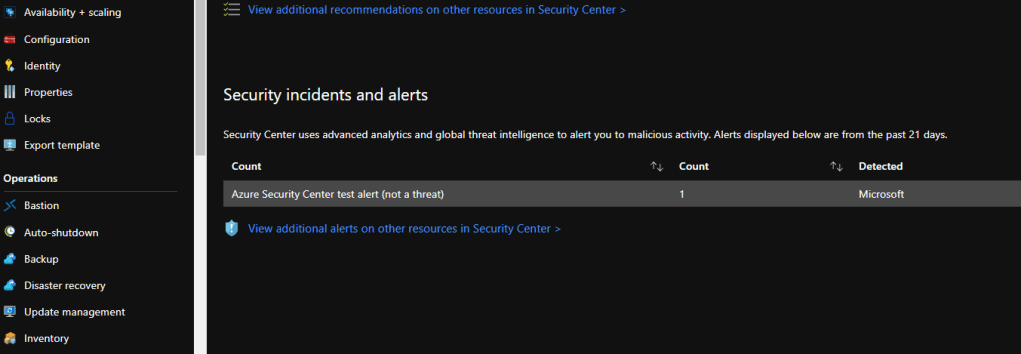
Testing setup
For testing we use Linux VM and ”eicar” alert example provided by Microsoft Validate alerts on Linux VMs
cp /bin/echo ./asc_alerttest_662jfi039n;./asc_alerttest_662jfi039n testing eicar pipe
Steps of the demo
- Member (operator) of the Security Group receives the alert
2. Operator opens the notification and submits the triage
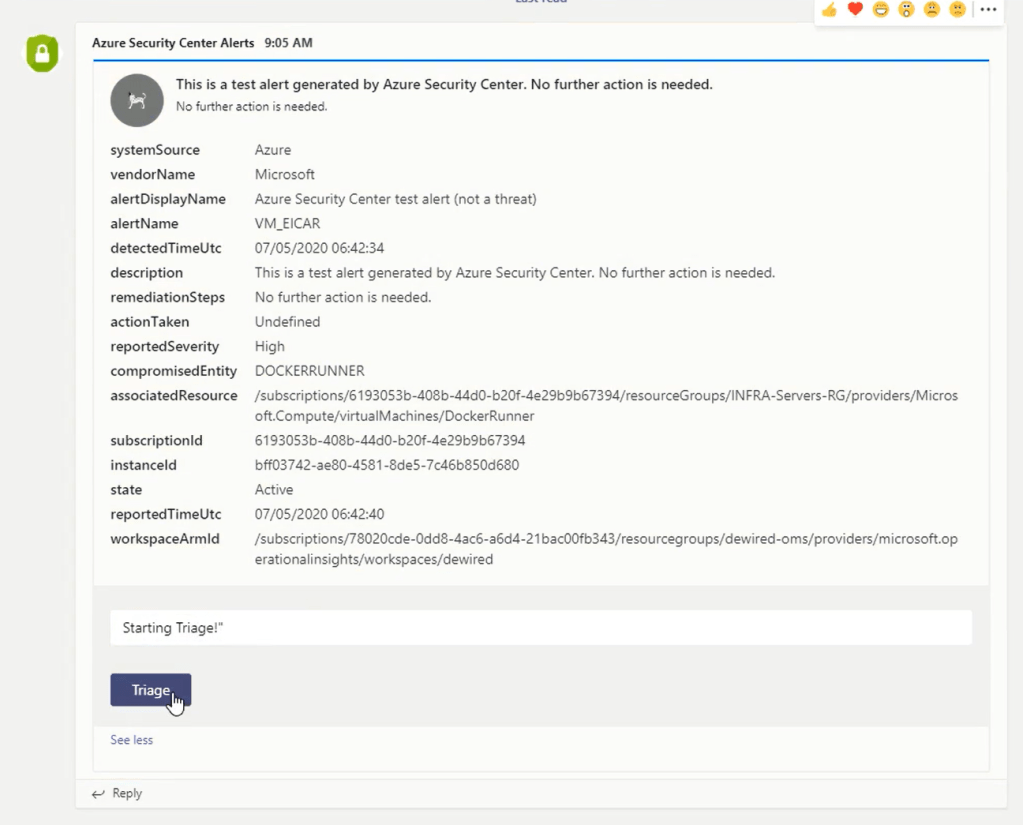
3. Triage button takes user to the affected resources security pane
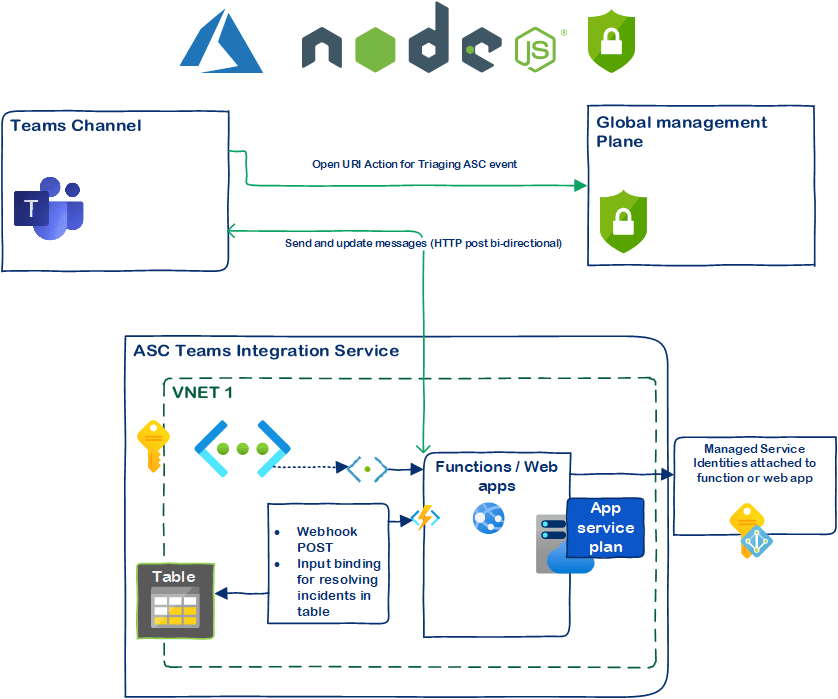
POC and architecture
For PoC I wanted test opening URI’s with MessageCard Actions. For this I lazied and used my existing ”AzExpress” test platform, which has Security Center API already. Once I proof the PoC the Architecture might look like this:
Ending words.
From here I will continue by creating further PoC matching the architecture above – Will also appreciate any input regarding what is useful information for the teams message for security operator to start the triage?
- As disclaimer its good to understand, that there exists complete SOAR platforms, such as what Microsoft is now Offering around Sentinel, Security center and Logic Apps. Feature in this blog is really just about testing quick actions and reactions via modern communication and team work medium, such as MS Teams.
- Using webhooks in MS Teams has some security implications, and I shall address those in further parts
- My daily work revolves around Azure and due to this, I find myself sometimes discovering ”new” things productivity side. One of these ”things”, is the versatile extensibility of MS teams 🙂 – If you have any good ideas as using teams for security teams go-to-place for communication, don’t hesitate to ping!
To be continued!
Br, Joosua
Paluuviite: MS teams and security center! – 365 admin service
are you sharing the code?
TykkääLiked by 1 henkilö
Hi! Most definitely will, as I get to POC part1. Stay tuned! and thx for asking
TykkääTykkää
Hi, I’ve now made the code available for deploying this into test environments https://securecloud.blog/2020/08/06/complete-guide-for-integrating-azure-security-center-alerts-2-ms-teams/
The functions code is git clone https://github.com/jsa2/ascintegration (I recommend, that its deployed together with the guide available in the blog post)
TykkääTykkää
Paluuviite: Complete guide for Integrating Azure Security Center Alerts 2 MS Teams! – SecureCloudBlog