While its not yet configurable in GUI, you can already today configure (with proper prerequisites) the preview for Security Graph API and Log Analytics Integration.
Side note: Similar Integration can be done for Event Hub, and its recommended while enabling LA integration to enable EH integration (if EH exists in tenant)
https://docs.microsoft.com/en-us/graph/security-qradar-siemintegration
While its not yet configurable in GUI, you can already today configure (with proper prerequisites) the preview for Security Graph API and Log Analytics Integration.
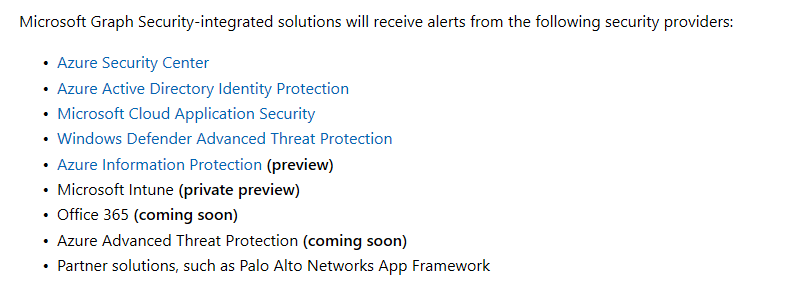
Alerts today include (Check link for original reference)
I will avoid using the word Azure Monitor here, as this integration is not really in my opinion tapping into any resource API in the Azure Monitor (unless you consider Azure Monitor as umbrella term

integration includes also Event Hub – which has been available for a good while already via similar method
Before proceeding: As always – read the disclaimer in the bottom of the page) I put the disclaimer up also here to emphasize its matter, not just as an escape clause
How To: integration with Log Analytics
- Disclaimer: The behavior may vary per tenant
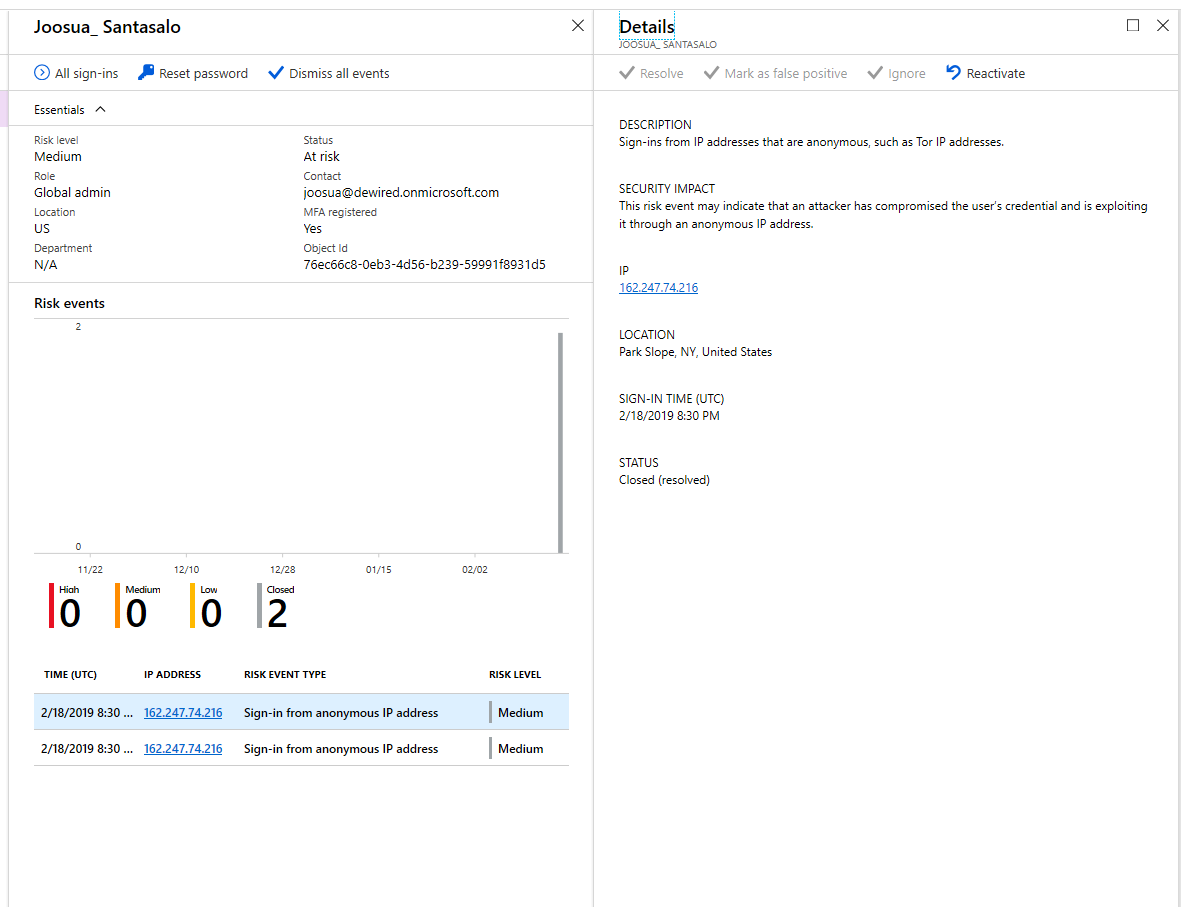
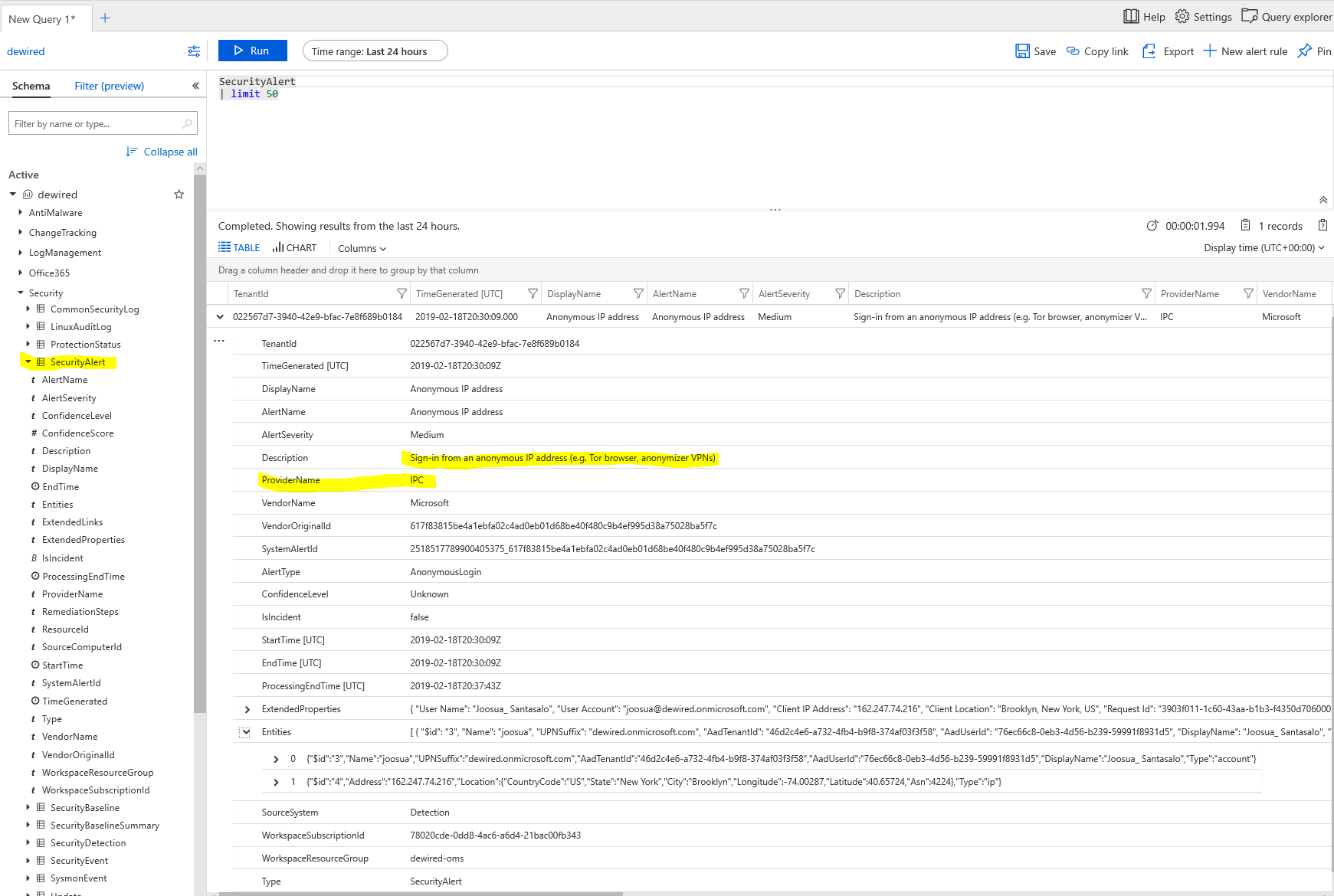
- It took few hours till events started popping up in Log Analytics and event hub
- To enable the integration You can use existing AAD tokens in cache to achieve this
-
- I’ve usually preffered the ADAL libraries to do this bit more simply, but in this case we want to use the AzureRM module to populate parts of the script simply (/done similarly here)
Login-AzureRmAccount
$ctx =Get-AzureRmContext
Get-AzureRmSubscription | Out-GridView -PassThru |Set-AzureRmContext
$rmEndpoint ="https://management.azure.com/providers/Microsoft.SecurityGraph/diagnosticSettings/securityApiAlerts?api-version=2017-04-01-preview"
#Details from IAM API
$Token = Invoke-RestMethod "https://login.windows.net/common/oauth2/token" -Method POST -Body @{
grant_type="refresh_token"
refresh_token = ($ctx.TokenCache.ReadItems() | Out-GridView -PassThru ).refreshToken
content_type = "application/json"
resource="https://management.core.windows.net/"
}
$json = '
{
"location": "",
"properties": {
"workspaceId": null,
"name": "securityApiAlerts",
"serviceBusRuleId": "/subscriptions/SUBSCRIPTION_ID/resourceGroups/RESOURCE_GROUP/providers/Microsoft.EventHub/namespaces/EVENT_HUB_NAMESPACE/authorizationrules/RootManageSharedAccessKey",
"logs": [
{
"category": "Alert",
"enabled": true,
"retentionPolicy": {
"enabled": true,
"days": 7
}
}
]
}
}
' | ConvertFrom-Json
$json.properties.serviceBusRuleId = ( (Get-AzureRmResource | where {$_.ResourceType -match "Eventhub"}| Out-GridView -PassThru).resourceID + "/authorizationrules/RootManageSharedAccessKey")
$json.properties.workspaceId = ((Get-AzureRmOperationalInsightsWorkspace | Out-GridView -PassThru ).resourceID)
$data = Invoke-RestMethod -Uri $rmEndpoint -Method Put -Body ($json | ConvertTo-Json -Depth 4) -UseBasicParsing -Headers @{
Authorization = ($Token.token_type) +" "+ ($Token.access_token)
} -ContentType "application/json; charset=utf-8"
Comment from @samilamppu
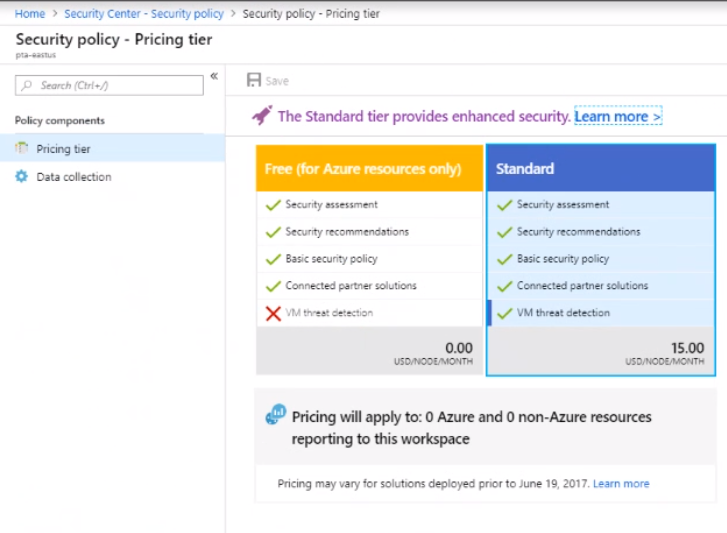
its quite likely, that you need to have Security Center Standard with proper event coverage enabled, to get the Node for security alerts under LA

Br,
Joosua

0 comments on “Enable Microsoft Security Graph Alerts in Log Analytics”